What's Your Risk from
Autonomous AI Security Posture Management (AI-SPM)
AI-SPM
For AI Security Posture Management via
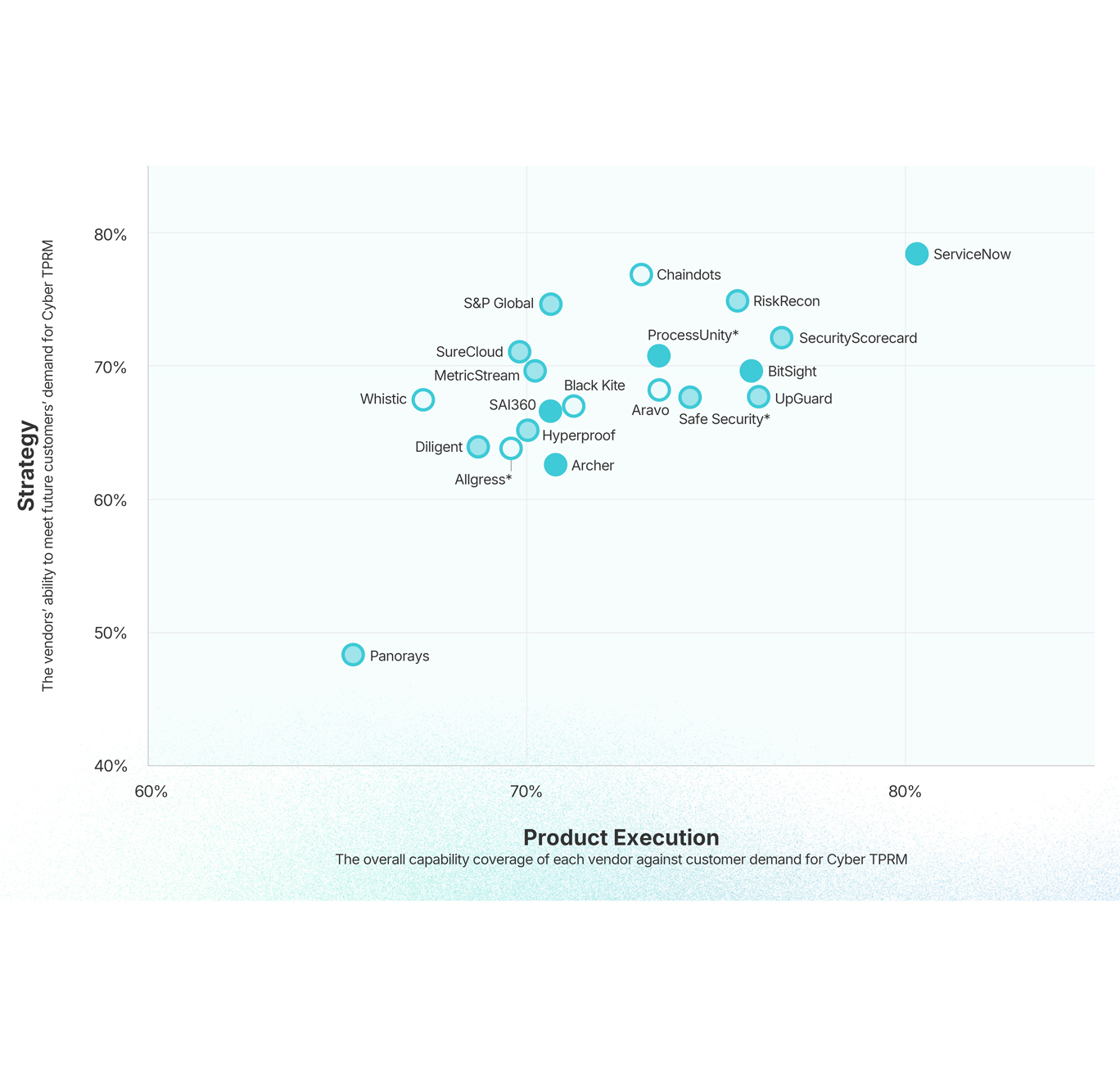
Third Party Risk Management
TPRM
For Vendor Cyber Risk Management via
Third Party Risk Management
CTEM
For Operational Cyber Risk Management via
Threat Exposure Management
CRQ
For Strategic Cyber Risk Management via
Cyber Risk Quantification
10% of Fortune 500 put AI to work with SAFE
Measurable Impact
Organizations using SAFE see:
AI-SPM
AI Security Posture Management
100%
Visibility to key vendor risk exposure
45%
Less time spent in compliance gap discovery
28%
Quicker risk burndown from AI solutions
TPRM
Third Party Risk Management
100%
Critical Vendor Coverage with Continuous Monitoring
66%
Time saved per Vendor Assessment
25%
Faster risk burndown of Vendor Exposures
CTEM
Continuous Threat Exposure Management
200%
Productivity improvement for triage, ticketing & validation
70%
Reduction in Critical Exposures on a Daily Basis
40%
Reduction in Mean Time to Remediate (MTTR)
CRQ
Cyber Risk
Cyber Risk
Quantification
73%
Reduction in Assessment & Reporting Time
33%
Faster risk burndown with same budget
20%
Saved on Cyber Insurance Premiums
Seamlessly connect your controls to SAFE
150+ native integrations. Zero friction.
With Enterprise-grade AI you can Trust
100+
Out of Box Agentic Workflow Templates
50+
Gen AI Agent Nodes
1
Enterprise Grade Agentic Trust Framework
Choose Demo
Select a demo to view
AI Security Posture Management (AI-SPM)
Third Party Risk Management (TPRM)
Continuous Threat Exposure Management (CTEM)
Cyber Risk Quantification (CRQ)
Experience SAFE Yourself
Take a self-guided demo now