FAIR Risk Assessment Examples: The Basics of a FAIR Assessment
Upgrade from a limited, manual approach to automated cyber risk quantification
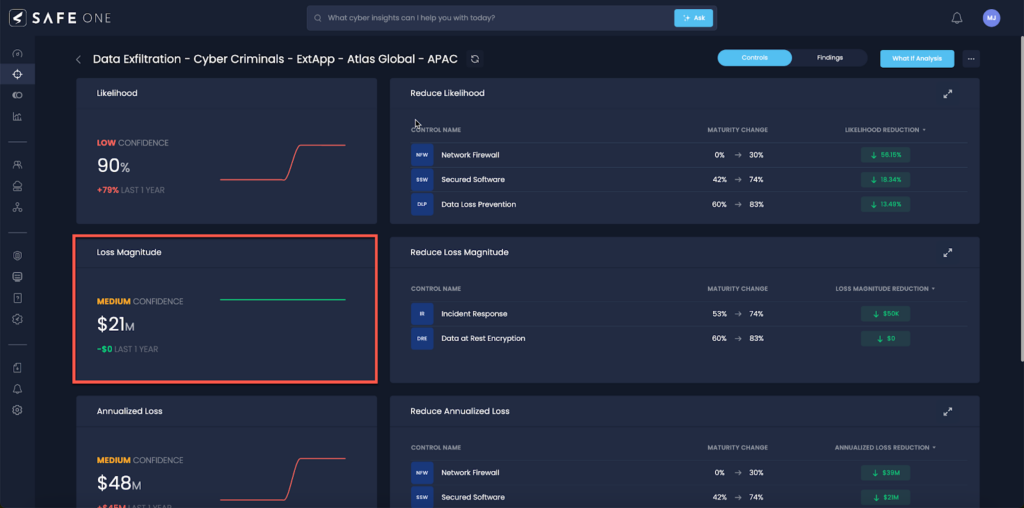
Cyber risk scenario analysis on the SAFE One platform
The SAFE One platform automates cyber and technology risk analysis and risk assessment based on Factor Analysis of Information Risk (FAIR™), the standard for risk quantification.
What does a FAIR risk assessment example look like? Here’s a quick guide to the process.
Formerly, risk analysts carried out these steps in a manual way by painstaking data collection, interviewing experts in the organization and filling out spreadsheets, chores that could take weeks.
SAFE’s innovation: The SAFE One platform, purpose built on FAIR, pulls together all the necessary elements in FAIR analysis to deliver continuous AI-powered cyber risk management in a unified view and, importantly, in a context valuable to business decision-makers.
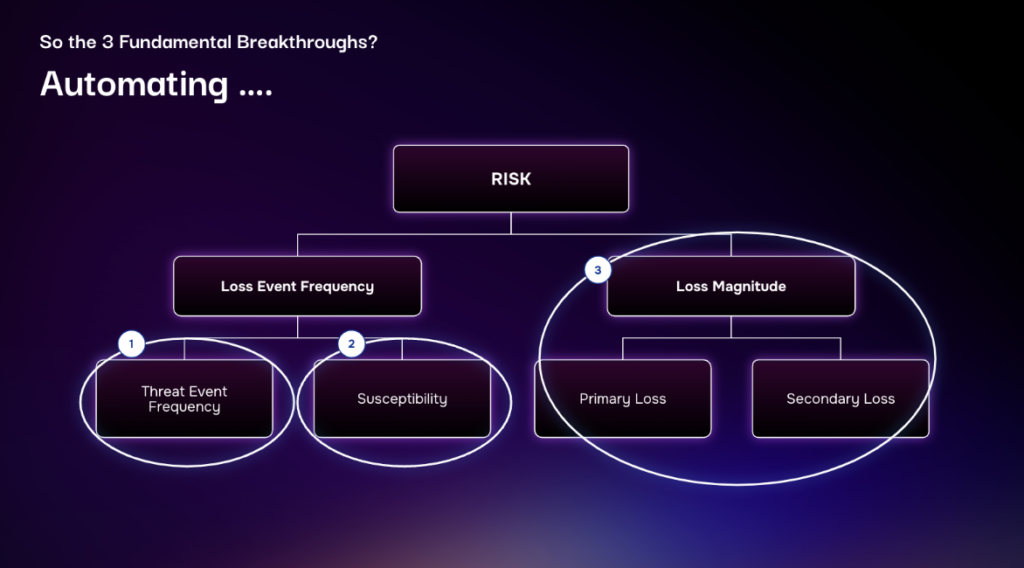
Basically, FAIR cyber risk analysis breaks down risk into factors that can be quantified to estimate the likelihood and probable impact of loss, the two high-level factors that decision makers must weigh in reacting to a risk.
But before we can start filling in the factors with numbers, we need to clarify or “scope” a loss event we want to analyze.
Step 1: Scoping a Risk Analysis
To scope an analysis, we first define the business decision we are trying to support (say, how to justify or prioritize security budget investments), then identify the relevant asset (a customer information database, an ecommerce application, etc.), then focus on the probable threats (insiders, criminal hackers), the type of loss that concerns us (confidentiality, availability, integrity) and exactly how the loss would take place, summed up in a loss event or risk scenario.
Here is an example risk scenario:
“Analyze the risk associated with a privileged insider intentionally disclosing the information contained in our customer relationship management database.”
SAFE’s Innovation – Risk Scenario Library
The SAFE One platform offers an out-of-the-box Risk Scenario Library with a wide range of pre-defined risk scenarios to expedite the risk assessment process. Scenarios are all FAIR-compliant, meaning you can’t go off track.
Step 2. Data Collection
With the specifics of our loss event scenarios set, we’re ready to plug in the data we need for analysis. In the manual approach, weeks might go by while an analyst hunts down datasets in various corporate silos or waits for calendar time with a subject matter expert.
SAFE’s Innovation – Data Feeds for a Continuous, All-Around View of Risk
This chart shows the FAIR factors we need data to quantify to roll up to our overall risk quantification.
>>Threat Event Frequency (the “outside-in” view of risk posture). The SAFE One Threat Center integrates over 25 daily threat feeds and integrations with threat intelligence from ISACs and from the dark web to enable the clearest outside-in view of an organization’s risk posture.
>>Susceptibility to Attack (the “inside-out” view of risk posture). SAFE supports 100-plus API integrations from vendors like Wiz and CrowdStrike. Deeply embedded AI processes signals and SAFE runs continuous analysis of control status and effectiveness with the FAIR Controls Analytics Model (FAIR-CAM). Also, an AI-driven questionnaire marketplace ingests NIST, ISO, HIPAA data on the organization to assess the strength of the controls stack.
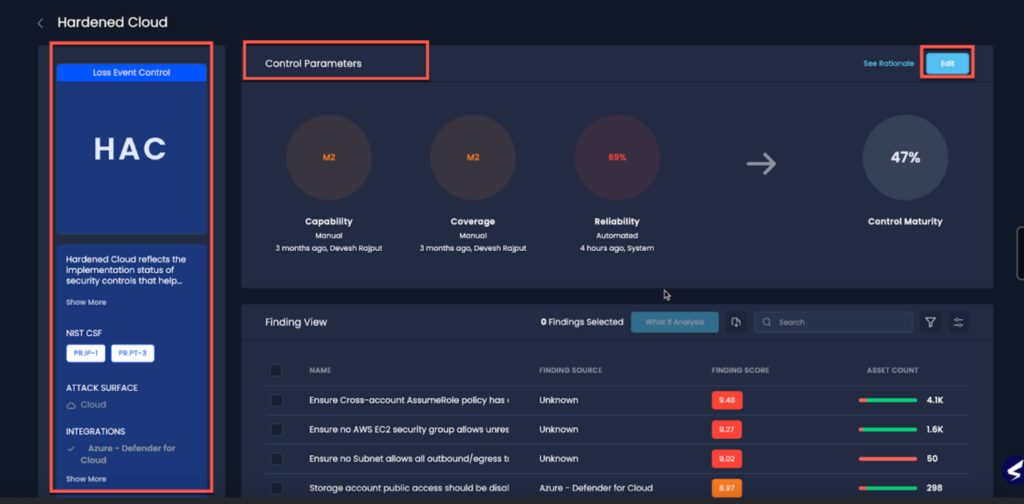
Controls analysis, SAFE One platform
>>Loss Magnitude. The SAFE One platform provides default values for a wide range of loss drivers, based on data from some of the largest insurance companies, all filtered through the FAIR Materiality Assessment Model (FAIR-MAM). A GenAI assistant reviews any custom data from the customer to keep everything aligned.
Step 3. Run FAIR Cyber Risk Analysis with Rapid Risk Assessment
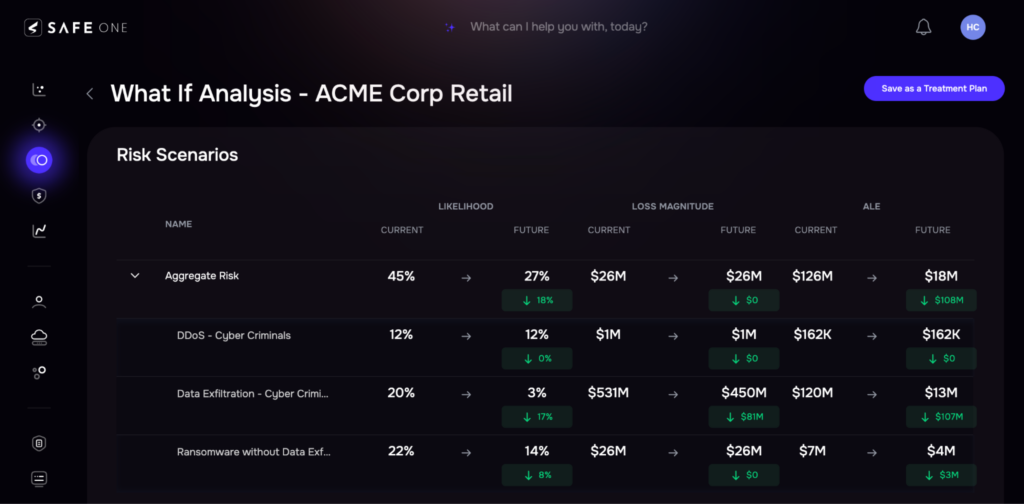
Traditional, manual FAIR analysis produced results for risk scenarios one at a time, for a siloed, point-in-time view of risk. SAFE has radically upgraded cyber risk analysis to a wide-aperture, continuous process.

SAFE’s Innovation – Unified View of Risk
SAFE One enables CISOs and other cybersecurity risk leaders to measure and visualize first-party, third-party, and emerging risks on a single platform and in real-time.
What’s more, the SAFE cyber risk management platform presents a coherent, business-friendly approach to cyber risk, so stakeholders can know and understand cyber risk:
>>Know your business units, processes and assets. Know your attack surface in detail.
>>Understand the top risk scenarios the organization faces, based on likelihood and probable magnitude.
Step 4. Report on Risk to Stakeholders, the C-Suite or the Board
SAFE provides dashboards specific to personas (board member, CFO, CEO, etc.) presenting data on a need-to-know basis. Users can view results from specific risk scenarios, or see risk aggregated to business units or even the entire enterprise. The system can deliver alerts if risk passes certain thresholds.
SAFE’s Innovation – Decision Support Based on FAIR Risk Assessment
SAFE doesn’t just report on risk – it recommends tactical and strategic responses to risk.
Findings scores highlight higher risk based on business impact, exploitability and other measures enabling prioritization of vulnerabilities based on more than narrow technical standards
You can accept a risk and give an exception or tag it for mitigation and assign it to a technical team.
On the strategic side, platform users can view progress in reducing risk over time, as well as conduct “what if” analysis, focussing on one control, for instance and testing the effect on risk reduction of investing to strengthen the control. What-if also can be used to evaluate the entire security budget for ROI.
FAIR Risk Assessment Example
Get a detailed picture of how FAIR risk assessment guided informed decision-making for this SAFE client:
SAFE Case Study
Find the ROI of Cybersecurity Tools – Mini Case Study
Let us show you the combined power of FAIR quantitative cyber risk analysis and the SAFE cyber risk management platform. Contact us for a demo.


