Why Traditional TPRM Fails Healthcare Providers and What Needs to Change

In healthcare, a vendor breach is a clinical crisis. When a supplier goes dark, the impact ripples beyond security; it disrupts prescriptions, billing, and ultimately patient care.
The Change Healthcare attack proved this, forcing hospitals and pharmacies into manual workarounds and delaying essential care. CMS has since urged health plans to prioritize business continuity over rigid filing requirements.
Standard vendor compliance isn’t enough. For healthcare providers, TPRM must protect three critical pillars: PHI, clinical operations, and care continuity.
Why Healthcare Third-Party Risk Is Different
Verizon’s 2025 DBIR makes the risk clear: ransomware-led intrusions are now the top cause of healthcare breaches, while third-party involvement doubled from 15% to 30%. Supply chain attacks are no longer isolated vendor issues — they can disrupt providers and expose patients at scale.
This changes the model for vendor risk for healthcare providers. A vendor should not be tiered solely by contract value, questionnaire score, or SOC 2 report. It should be tiered by how it affects care delivery.
A low-spend vendor that supports radiology scheduling, prescription processing, telehealth, medical transportation, or patient communications may create more operational risk than a high-spend back-office vendor. A billing or clearinghouse partner may not touch bedside care, but its outage can still threaten cash flow, practice operations, and patient access.
Learn how global healthcare providers are implementing a new, autonomous TPRM Model
HIPAA Vendor Risk Assessment Is Necessary, But Not Enough
HIPAA already makes continuous third-party oversight a core requirement. HHS defines a business associate as an entity that performs functions or services involving the use or disclosure of protected health information on behalf of a covered entity. HHS also requires covered entities to obtain written assurances, typically through Business Associate Agreements, that business associates will appropriately safeguard PHI.
The HIPAA Security Rule also requires an accurate and thorough assessment of risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI. HHS specifically notes that organizations should identify external sources of ePHI, including whether vendors or consultants create, receive, maintain, or transmit ePHI.
But healthcare providers need to go further: A BAA can define obligations. A questionnaire can capture controls. An annual review can document oversight. But none of those automatically answers the questions that matter during a live vendor incident:
- Can this vendor outage delay patient care?
- Which clinical workflows depend on this supplier?
- Which systems exchange PHI or ePHI with them?
…and so on
This is where TPRM must move beyond compliance and become an operational resilience function.
The New Healthcare TPRM Playbook
A modern healthcare TPRM program should be built around care continuity, not just control coverage.
1. Discover every vendor, business associate, subcontractor, and shadow dependency
Healthcare providers often have thousands of third parties across EHRs, cloud services, claims, billing, revenue cycle, clinical applications, labs, imaging, staffing, medical devices, remote monitoring, facilities, and outsourced services.
The first step is knowing who exists, who touches PHI, who supports clinical workflows, and who has downstream subcontractors.
SAFE TPRM enables automatic discovery of shadow vendors and subcontractors (fourth parties). SAFE then automatically classifies and tiers the vendors, and surfaces contract gaps to reduce missed or misclassified vendors with predefined Agentic workflows.
2. Tier vendors by patient impact, not just spend
Healthcare vendor tiering should include:
- PHI or ePHI access
- Clinical workflow dependency
- EHR, pharmacy, imaging, lab, or claims connectivity
- Network or privileged access
- Medical device or cyber-physical system exposure
- Outage impact on care delivery
- Concentration risk and availability of alternatives
- Subcontractor and fourth-party dependency
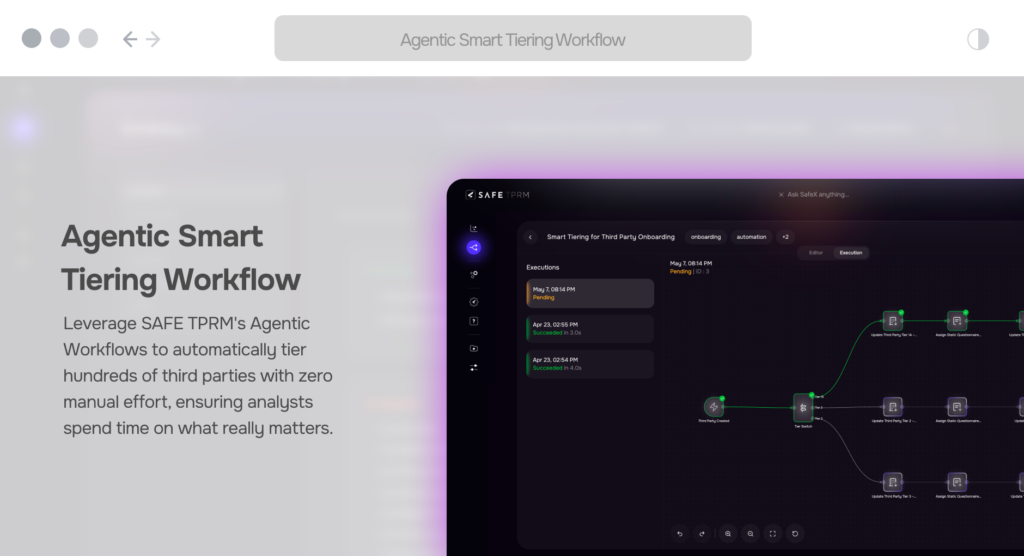
This helps TPRM teams identify vendors that are patient-critical, not just contractually important. SAFE smart tiering Agentic workflow tiers (and re-tiers) vendors based on business context, metadata, data access, business dependency, and more – all without any manual effort.
See how SAFE’s Smart Tiering Agentic Workflow works
3. Continuously monitor vendor risk, not annually review it
Annual assessments were never designed for ransomware speed. Verizon found ransomware present in 44% of breaches reviewed in its 2025 dataset, up from 32% the prior year.
Healthcare providers need continuous monitoring for breach signals, leaked credentials, exploited vulnerabilities, exposed services, medical device vulnerabilities, and vendor posture changes.
SAFE TPRM continuously monitors breach feeds, leaked credentials, and exploited device vulnerabilities tied to vendor profiles to help detect compromise faster and reduce patient-care disruption. SAFE also instantly notifies and alerts the right owners to take action, which reduces delays when time is of the essence.
4. Make contracts and BAAs operationally useful
Healthcare contracts should not be passive documents stored for audit season. They should be actively analyzed for breach notification terms, audit rights, subcontractor requirements, data handling obligations, encryption expectations, recovery commitments, offboarding obligations, and incident communication timelines.
The goal is simple: when something happens, the provider should already know what the vendor is obligated to do, what evidence is required, who must be notified, and what decisions need to be made.
SAFE supports evidence and contract automation by parsing the document. By analyzing evidences in the document store and questionnaire assessment responses, SAFE can map the vendor’s risk posture to control status and provide HIPAA, Texas HB300, and ISO dashboards with audit-ready exports and breach-impact timelines.
5. Plan for supplier concentration and clinical downtime
TPRM teams should work with clinical operations, legal, procurement, IT, security, compliance, and business continuity teams to identify single points of failure. For each critical vendor, the program should define backup workflows, manual procedures, alternate suppliers, minimum recovery expectations, and decision criteria for disconnecting or reconnecting systems.
The AMA’s Change Healthcare guidance clearly captured this type of decision-making, advising healthcare organizations to evaluate the risks of using or severing connectivity with impacted systems, including potential loss of prior authorizations, electronic prescribing, and other patient care functions.
That decision-making will only get harder as AI accelerates vulnerability discovery and exploitation. Anthropic’s Project Glasswing showed how Claude Mythos Preview can identify previously unknown vulnerabilities across critical infrastructure, while Forrester warned that AI-led exploit discovery could compress the window from discovery to exploitation to minutes.
For healthcare providers, the takeaway is not just “patch faster.” It is: plan for downtime before downtime becomes a clinical crisis. Rick Howard’s Cybersecurity First Principles frames resilience as accepting that cyber events will happen and building the ability to survive them. If AI-assisted attackers increase attack volume by 10x or 100x, provider organizations need to be ready for a day when one to five critical suppliers are disrupted at once — from e-prescribing and claims to EHR integrations, labs, imaging, and patient communications.
SAFE enables healthcare teams to test more than vendor controls. It helps analysts answer: which vendors have redundancy and how quickly care teams can keep operating when a supplier goes dark.
Want a practitioner’s view on what is changing in TPRM? Watch the SAFE Cyber Risk Podcast episode with Vincent Scales, Lead Director, GRC at CVS Health, on why TPRM is hitting a breaking point — more vendors, more risk, and the same headcount.
6. Automate the work that slows TPRM teams down
Healthcare security and risk teams are rarely staffed in proportion to the size of their vendor ecosystem. Manual intake, chasing questionnaires, reviewing evidence, checking BAAs, tracking reassessments, and following up on remediation do not scale.
Forrester’s TPRM platform landscape notes that TPRM platforms can help catalog third-party relationships, consolidate risk and compliance data, automate processes from risk identification to corrective action, and strengthen ecosystem resilience.
This is where AI-first TPRM becomes practical. SAFE’s Agentic Workflows automate Business Associate onboarding, evidence collection, reassessments, and continuous monitoring across healthcare vendors, with additional focus on clinical and PHI-handling vendors. SAFE TPRM’s flexible, trigger- and action-based workflows reduce manual effort, eliminate process variability, and shorten third-party onboarding, assessment, and remediation cycles.
Teams can build workflows from scratch or leverage in-built templates, then tailor them to organizational policies, vendor risk tiers, and approval structures, enabling stronger oversight, faster decision-making, and measurable third-party risk reduction. When designed astutely, certain workflows will eliminate human intervention altogether, so analysts can focus energy on building programs to increase resilience for the time when breaches are an expected daily occurrence.
TPRM is Part of Healthcare Resilience
For healthcare providers, TPRM can no longer sit in a compliance silo. The right question is not only: “Did this vendor complete the assessment?”
The better question is: “Can we continue delivering care if this vendor is breached, degraded, or unavailable tomorrow?”
SAFE TPRM helps healthcare providers manage vendor risk across the full lifecycle — from discovery and onboarding to assessments, continuous monitoring, evidence review, contract analysis, remediation, and offboarding. With SAFE TPRM, healthcare providers can:
- Discover shadow vendors, contractors, and subcontractors accessing EHI
- Classify and tier vendors by PHI access, clinical dependency, and operational impact
- Continuously monitor breach feeds, leaked credentials, and exploited vulnerabilities
- Automate Business Associate onboarding, evidence collection, reassessments, and remediation workflows
- Map evidence to HIPAA, Texas HB300, ISO, and other control frameworks
- Identify concentration risks and vendor redundancies across critical clinical systems
- Generate audit-ready reporting and breach-impact timelines
The outcome is a TPRM program that supports compliance and is built for something bigger: protecting care continuity.