Calm the noise – get back to first principles in third-party risk management, Visibility, Prioritization and Scale

Security teams are now inundated with findings at a scale that outpaces human analysis, while third- and fourth-party ecosystems continue to expand the attack surface in ways that are difficult to map, let alone manage. See Project Glasswing by Anthropic for a dystopian look at what could be ahead.
In this environment, more alerts and more assessments do not inherently produce better decisions. In fact, they often have the opposite effect, creating noise, fragmentation, and delay. TPRM Program Death by Dashboards
At moments like this, the most effective CISOs don’t add complexity. They return to first principles.
At its core, third-party risk management comes down to three fundamental questions:
- Do we clearly see risk in terms the business understands?
- Are we consistently prioritizing what actually reduces that risk?
- Can we scale those efforts as our ecosystem and the threat environment grows?
As we talk to a broad range of CISOs, these questions surface in three persistent challenges: Visibility, Prioritization, and Scale. Each one compounds the others. Addressing them requires a shift from fragmented, manual approaches to a more unified, decision-driven model of cyber risk management.
1. Visibility: Seeing Risk in Business Terms
Most organizations still assess third-party risk through a mix of questionnaires, point-in-time assessments, and low-fidelity technical metrics. While these approaches generate data, they rarely produce clarity.
The result is predictable:
- Risk is described in qualitative or technical terms, not business impact
- Reporting is fragmented across dashboards and narratives
- Executive understanding varies—and often relies on contradictory interpretations
This creates friction at the worst possible moment: decision-making.
When risk is not expressed in financial or business terms:
- Board discussions stall on explanation instead of action
- Investment decisions are delayed or challenged
- Security struggles to articulate tradeoffs in a way the business understands
One CISO at a major company described their previous state this way:
“It could take up to three months to assess and communicate risk scenarios using spreadsheets.”
That lag doesn’t just slow reporting—it limits the organization’s ability to act on risk while it still matters.
What effective visibility looks like:
- Cyber risk quantified in business terms (loss exposure, likelihood, impact)
- A consistent, unified view of threats and risk across internal and third-party environments
- Executive-ready reporting that drives decisions, not debate
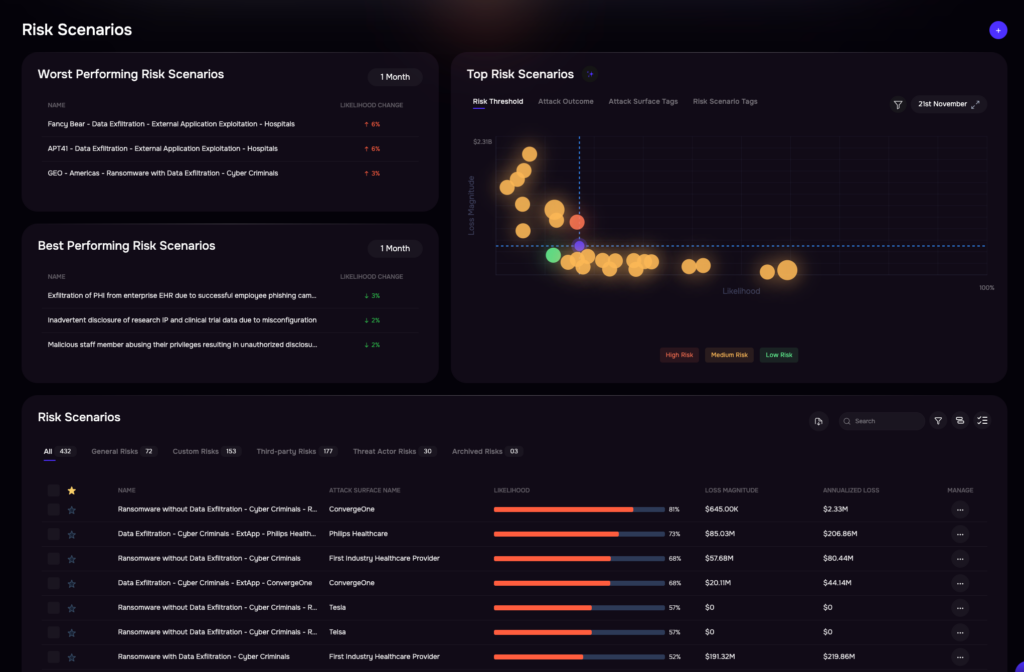
Quantitative cyber risk analysis with the SAFE One platform. Click for larger image.
2. Prioritization: Focusing on What Actually Reduces Risk
Even when organizations have visibility into issues, prioritization often breaks down.
Security teams are inundated with findings—vulnerabilities, misconfigurations, vendor reporting shortfalls—but lack a defensible way to determine what matters most. As a result:
- Remediation is driven by CVE scores, compliance mandates, or intuition
- High-volume issues crowd out high-impact risks
- Teams measure activity (patch tickets closed) instead of outcomes (risk reduced in dollar terms)
This leads to a dangerous pattern: significant effort with limited impact.
One security leader summarized the problem bluntly:
“We were spending time fixing issues that didn’t materially reduce risk.”
Without a clear connection between remediation and business impact:
- Critical risks remain exposed
- Leadership questions the value of security investments
- Budgets become harder to justify
What effective prioritization looks like:
- Remediation ranked by quantified business impact—not technical severity
- Clear linkage between actions and measurable risk reduction
- Continuous tracking of risk burn-down, not just activity volume
Organizations that shift to this model consistently report sharper focus. In one case:
“Teams moved from reactive remediation to proactive, risk-driven prioritization with product teams.”
3. Scale: Keeping Up Without Adding Headcount
The third challenge is structural. As businesses grow—adding vendors, technologies, and integrations—risk programs must scale accordingly.
But in many organizations, scaling still means adding people.
Current-state realities include:
- Heavy reliance on manual assessments and reviews
- Analysts spending significant time on repetitive, low-value work
- Programs forced to sequence work rather than operate continuously
The consequences are predictable:
- Coverage gaps emerge, especially across third- and fourth-party risk
- Risk insights become delayed or stale
- Teams experience burnout while leadership loses confidence in the program
A global organization managing vendor risk described their situation prior to transformation:
“We had a backlog of 600+ vendors, relying on manual assessments and external reviewers.”
That model doesn’t scale.
What effective scale looks like:
- Continuous, automated assessment and monitoring of third-party risk
- Autonomous workflows that reduce manual effort
- The ability to expand coverage without increasing headcount
In practice, organizations that modernize here see measurable impact:
- “Assessment cycles reduced from days to hours”
- “Over 30 hours eliminated from vendor assessment workflows in weeks”
- “Critical vendor coverage expanded from partial to continuous monitoring”
Bringing It Together: From Fragmentation to a Unified Model
Visibility, prioritization, and scale are not independent problems. They reinforce each other:
- Without visibility in business terms, prioritization is subjective
- Without prioritization, scale amplifies inefficiency
- Without scale, visibility and prioritization lose relevance
The underlying issue is fragmentation—of data, workflows, and decision models.
Leading organizations are addressing this by:
- Unifying cyber and third-party risk into a single model
- Continuously translating technical signals into business impact
- Automating assessment, prioritization, and remediation workflows
This shifts TPRM from a reactive, compliance-driven function to a continuous, decision-support capability aligned with the business.
The Goal: A New Operating Model for TPRM
The future of third-party risk management is not more questionnaires, more dashboards, or more analysts. It is a fundamentally different operating model:
- Continuous instead of periodic
- Quantified instead of qualitative
- Automated instead of manual
Organizations that make this shift report:
- Faster, more confident decision-making
- Clear alignment between security actions and business outcomes
- The ability to scale risk management without scaling headcount
If you’re evaluating how to move in this direction, it’s worth exploring platforms designed to unify cyber risk, exposure management, and TPRM—combining quantitative risk models, AI-driven prioritization, and autonomous workflows into a single system.
See how SAFE solves the most urgent problems of the CISO today. Learn more about SAFE — or schedule your demo now.


