SAFE One for Technology Providers
Managing cyber risk to protect the platforms the world runs on
Cloud adoption, APIs, SaaS sprawl, DevOps pipelines, and remote work have dramatically expanded the attack surface
Downtime, API failures, cloud incidents, and software supply-chain breaches can halt critical business systems
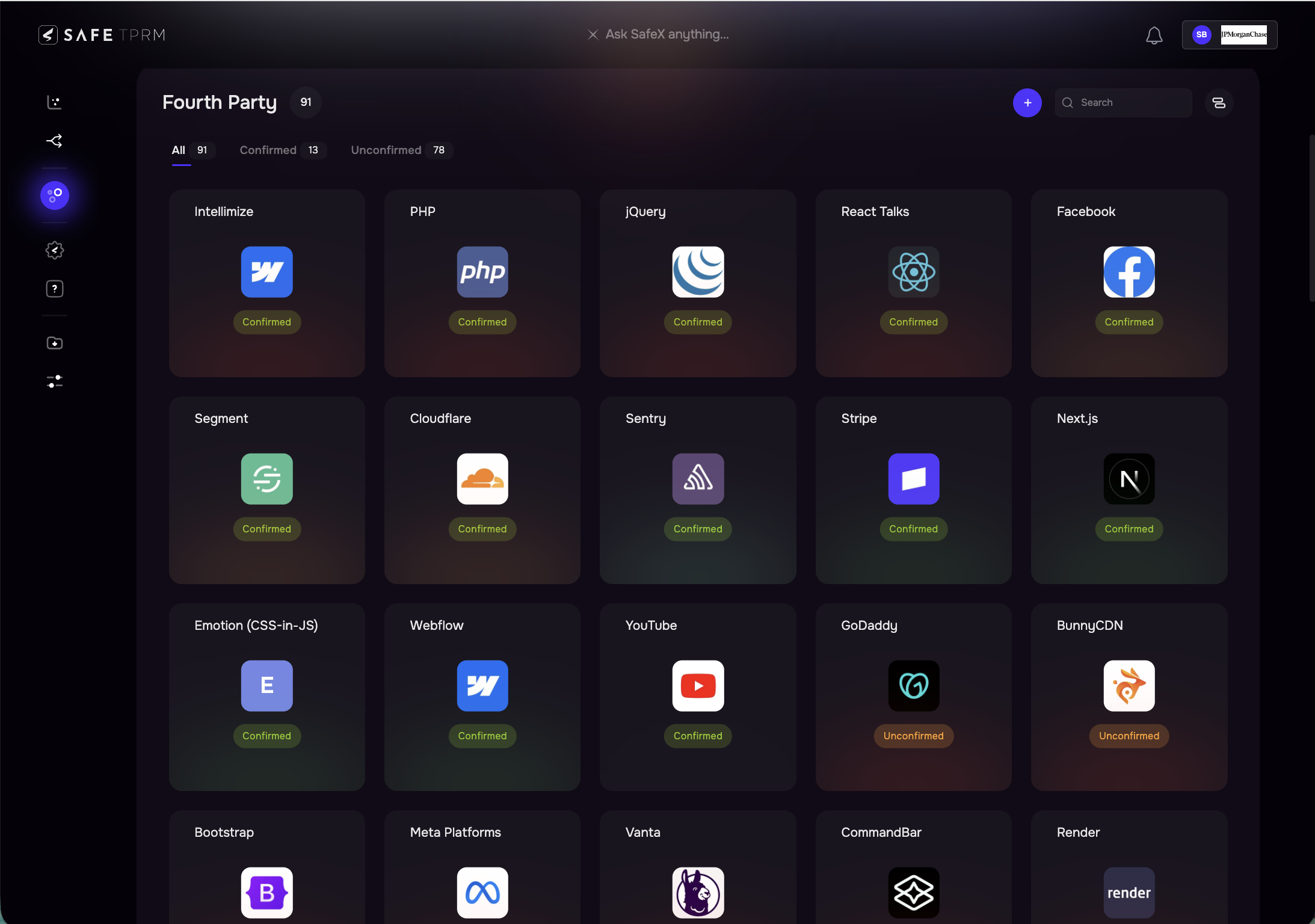
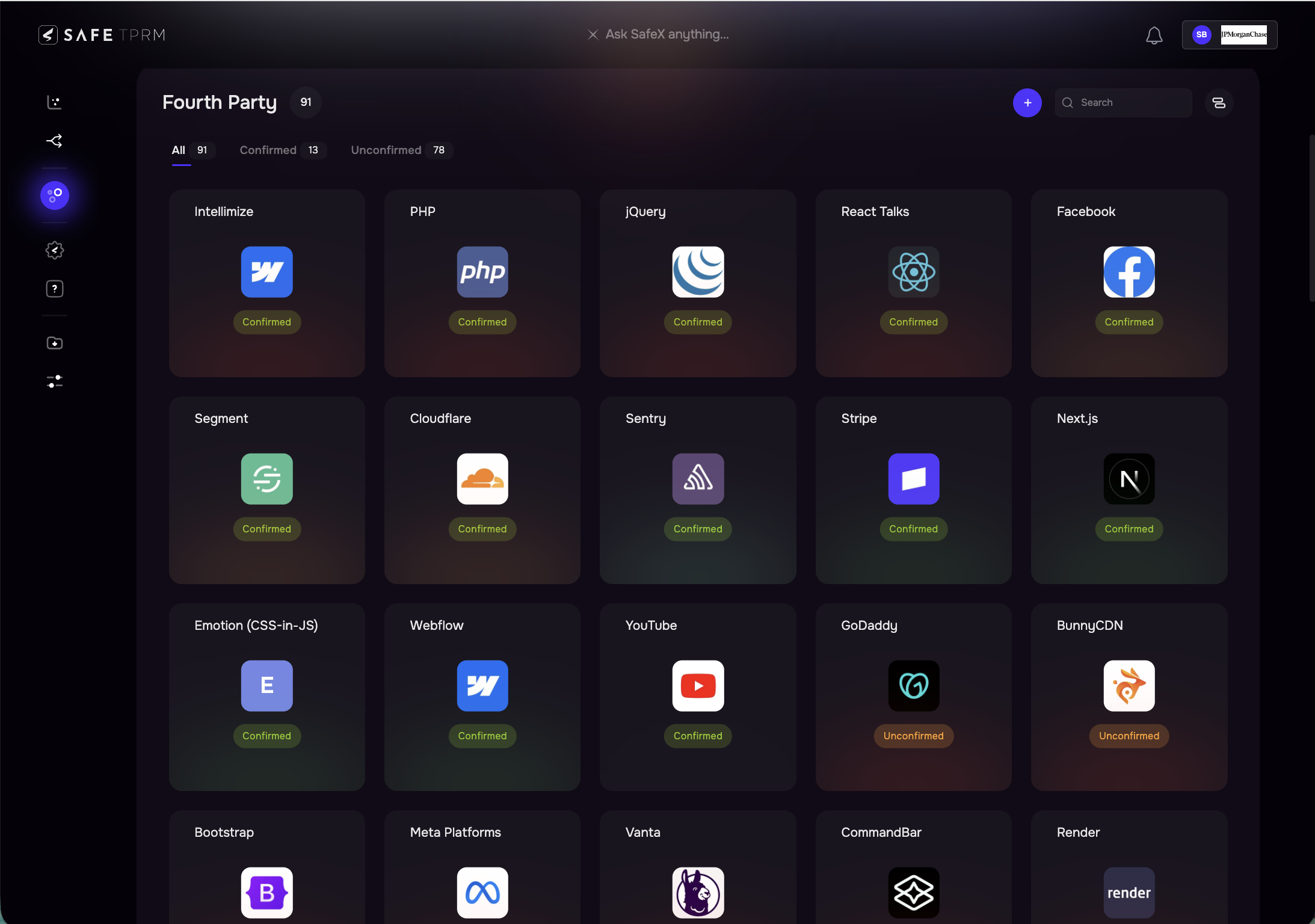
Reliance on open-source, cloud, and external developers introduces hidden supply-chain risks that legacy tools can’t detect
IT and security teams are overwhelmed with alerts, CVEs, & findings, yet lack a clear way to understand which issues matter most
Lean teams cannot manually track vendor risk, vulnerabilities, and configuration drift across large, complex environments



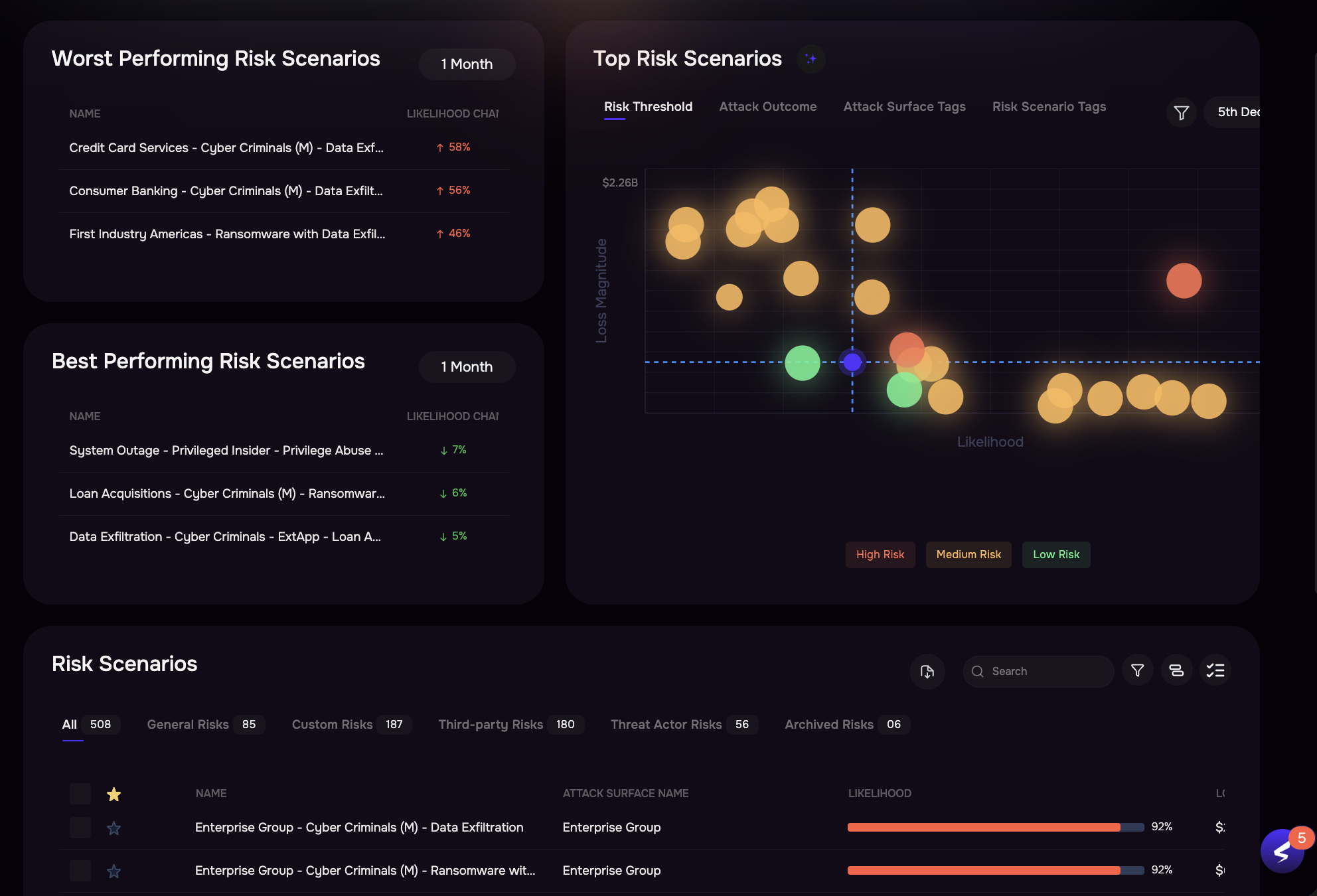

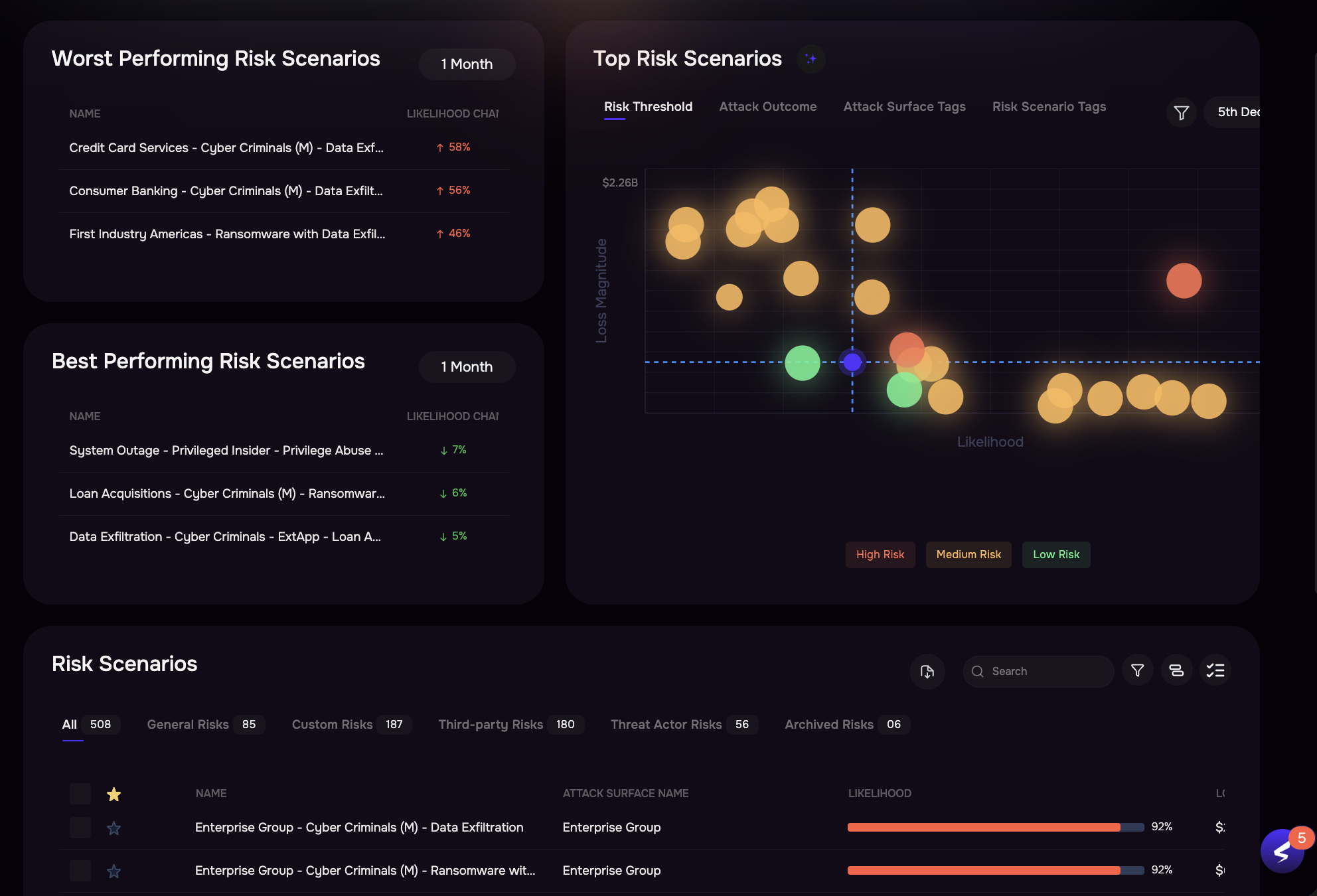


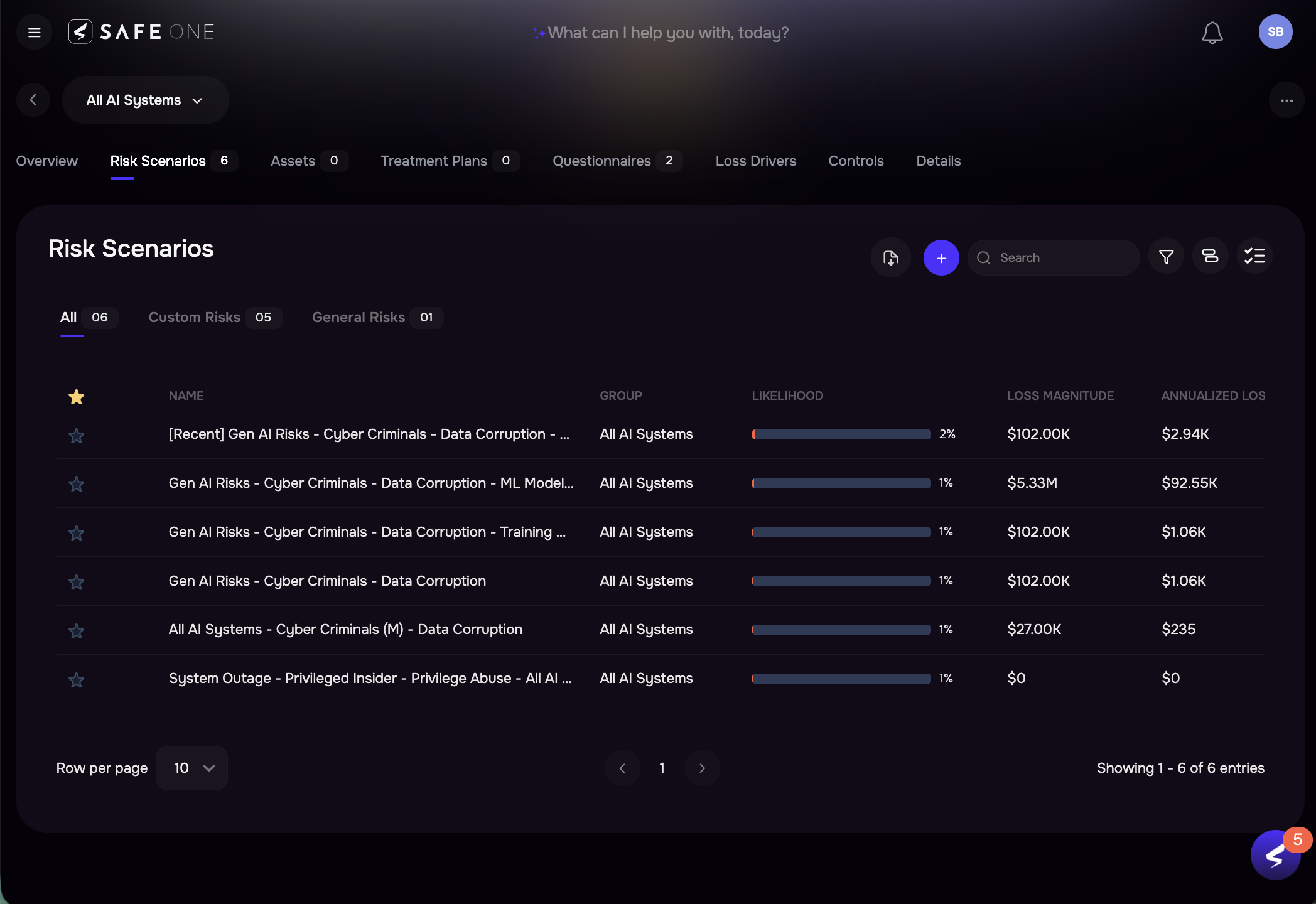

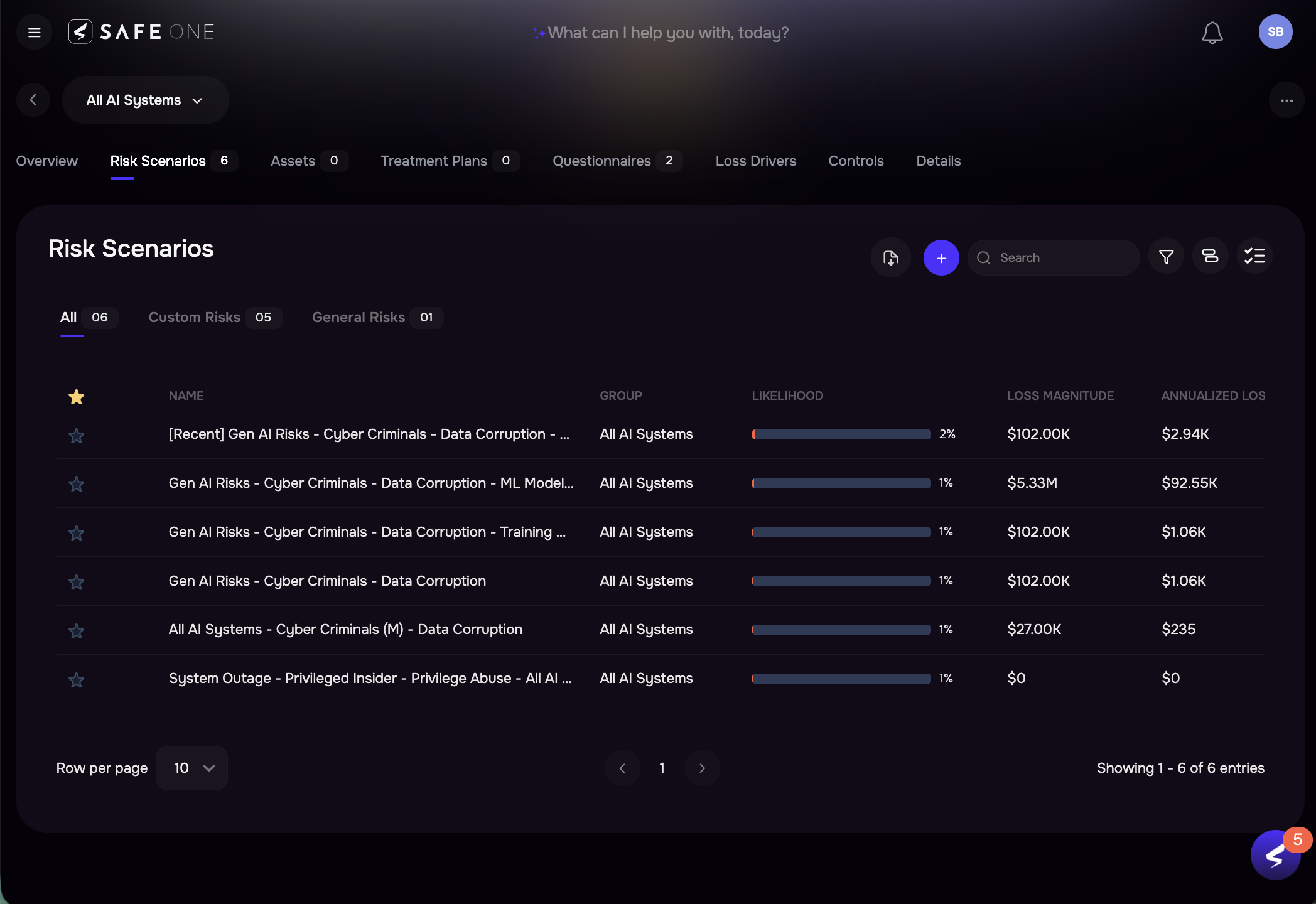
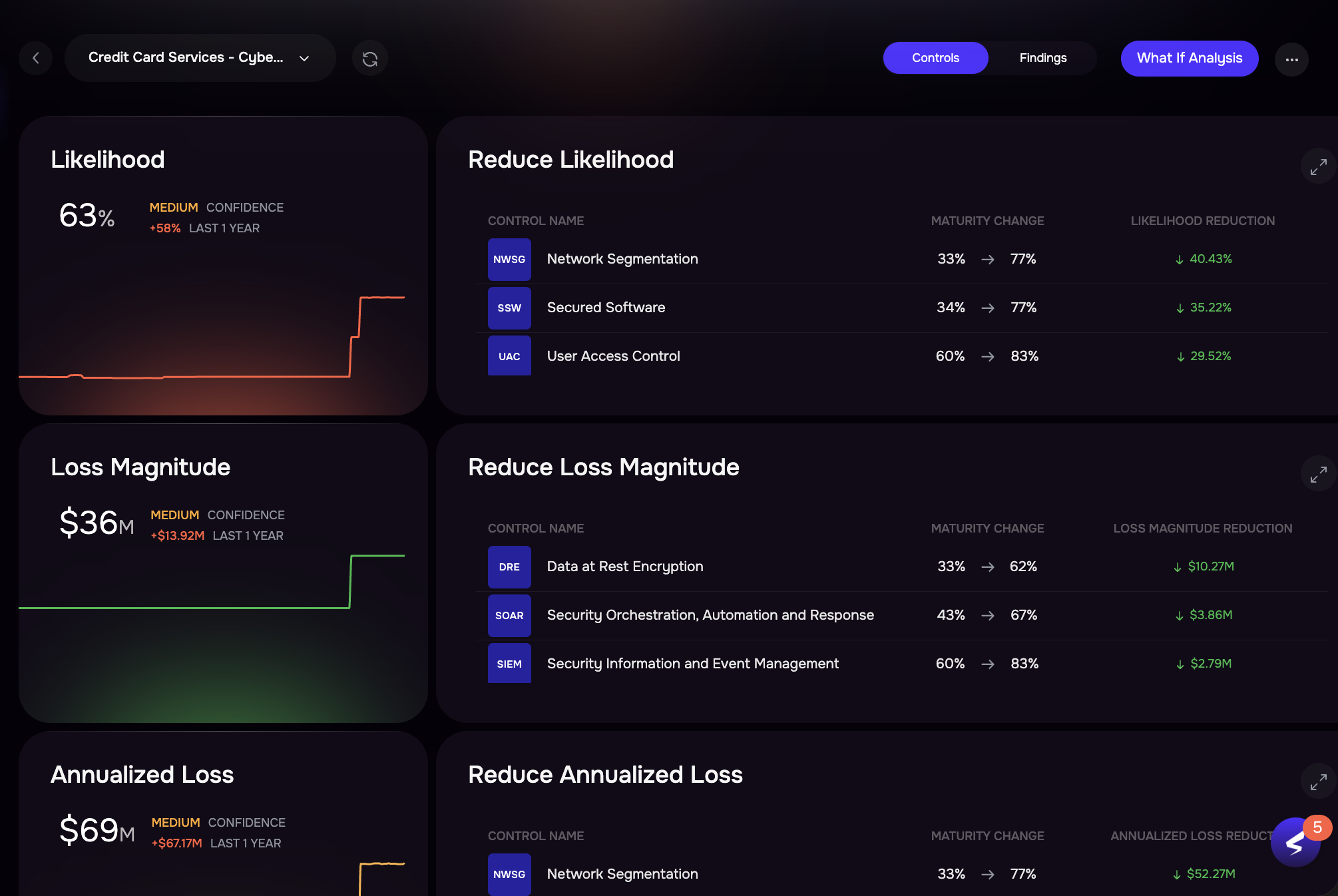

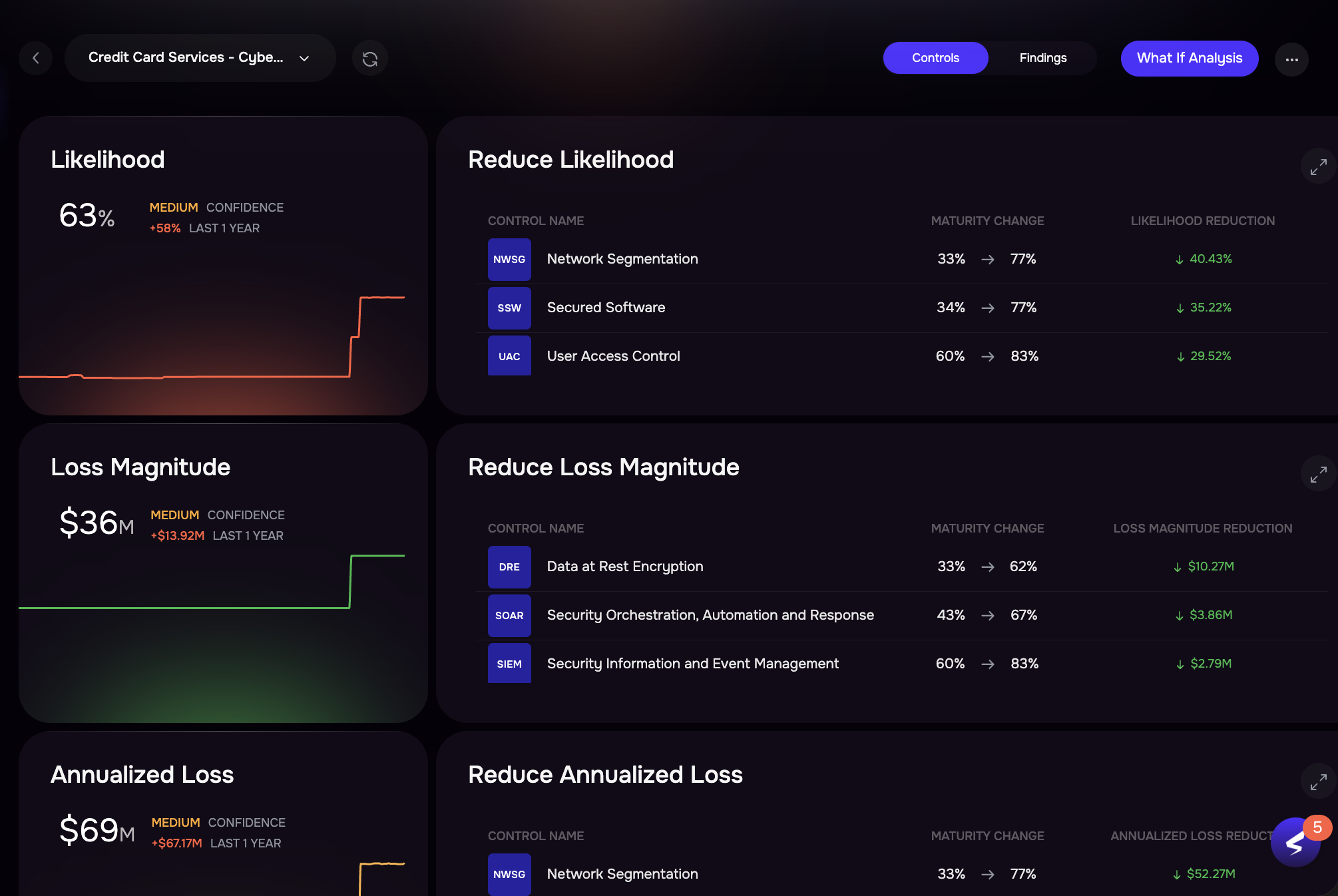

Lead with autonomous cyber risk management, real-time risk visibility, and ROI-driven remediation strategies that protect the business

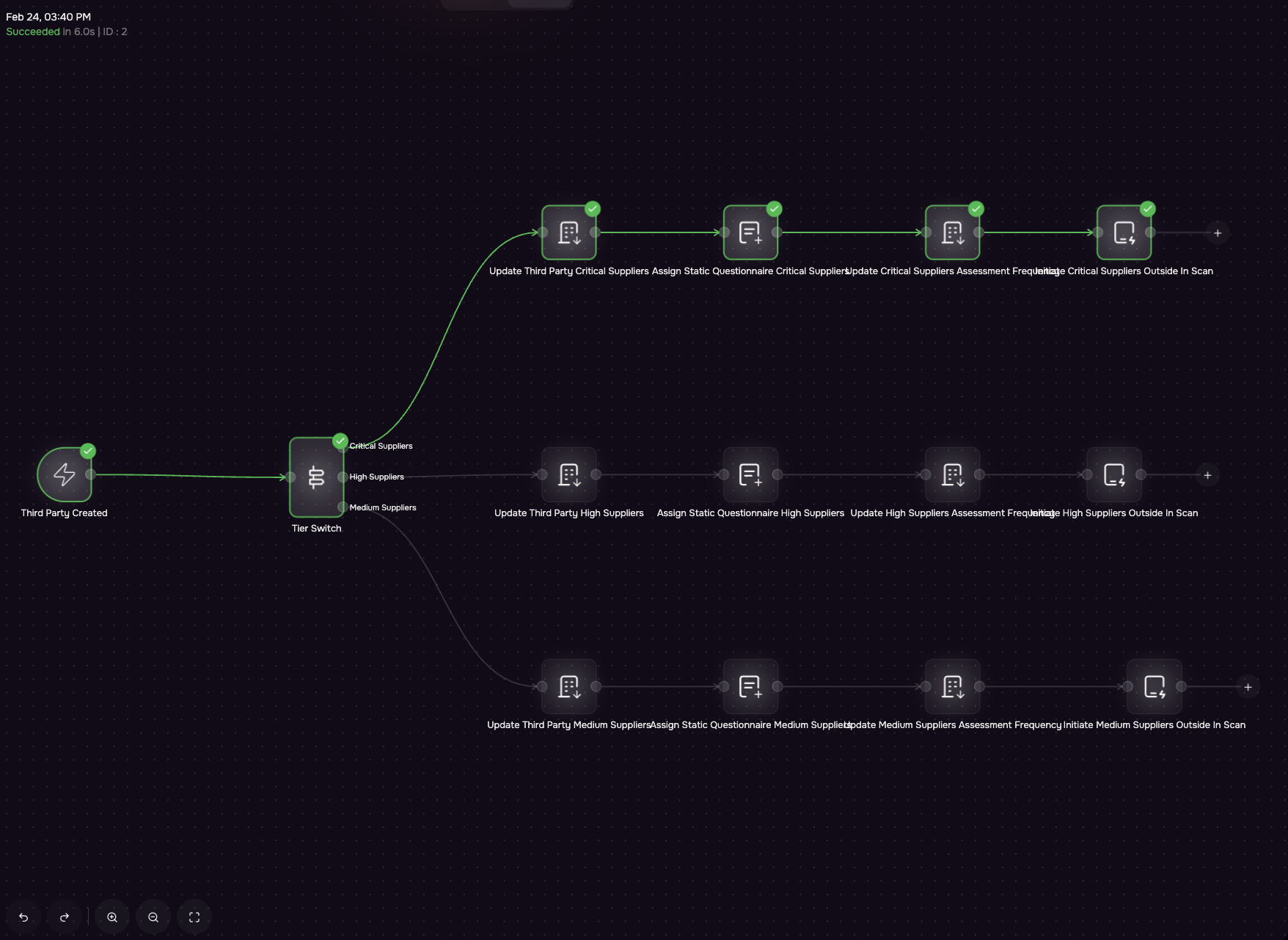
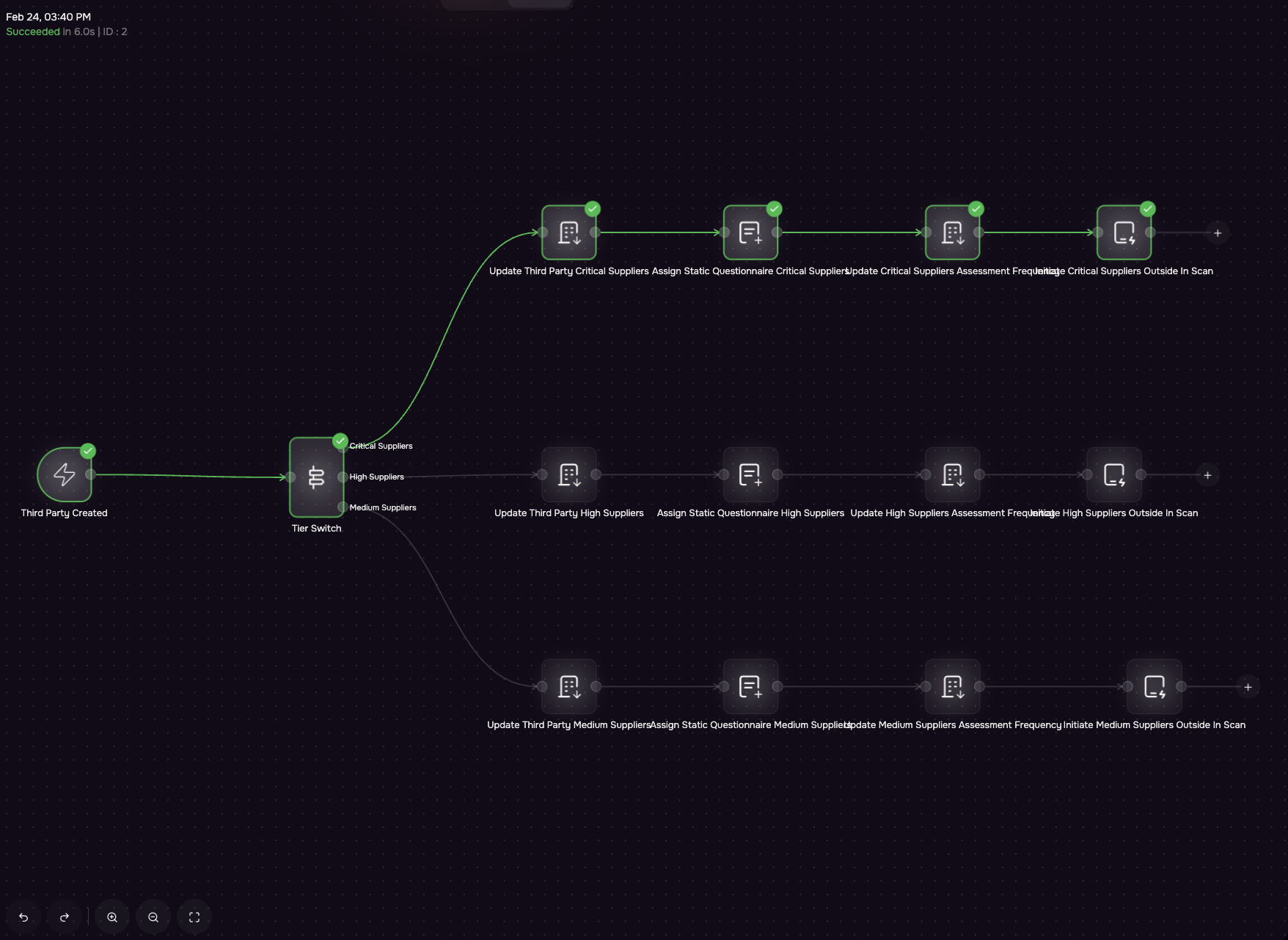
Build and scale a strategic TPRM program with automated workflows that identify, prioritize, and mitigate risks across critical partners

Minimize manual effort with autonomous TPRM so you can focus on high-risk issues and support quicker, more consistent assessments