Identify, assess, and mitigate similar exposures before they cost millions

Third-party vendors caused an estimated $12.5 billion in breach-related losses across Fortune 500 companies in 2023, yet most security teams still rely on annual questionnaires and compliance checkboxes to assess these risks. When a payment processor gets ransomware, a cloud provider suffers an outage, or a software vendor ships compromised code, the financial and operational damage cascades directly to every customer depending on that service.
This article examines eight documented third-party incidents from 2020-2026—from SolarWinds to CrowdStrike—and explains how to identify, assess, and mitigate similar exposures before they cost your organization millions in breach response, regulatory fines, and lost revenue.
What Is Third-Party Risk?
Third-party risk is the potential for financial loss, operational disruption, data breach, or compliance violation caused by an external vendor, supplier, contractor, or service provider that has access to your systems, data, or business processes. Organizations today depend on ecosystems of software vendors, cloud providers, payment processors, logistics partners, and professional services firms—when any of these external parties experience a security incident or operational failure, the consequences cascade directly to your organization.
The challenge comes down to three factors. First, third parties often hold privileged network access, process sensitive customer data, or run mission-critical applications on your behalf. Second, you can’t continuously monitor third-party security postures, patch cycles, or insider threats the way you monitor your own systems. Third, a breach or outage at a single widely used vendor can simultaneously affect hundreds or thousands of downstream customers—think of it as a force multiplier for attackers.
Third-party risk management (TPRM) is the systematic process of identifying, assessing, monitoring, and mitigating risks introduced by external business relationships. It’s the difference between reacting to vendor incidents after they’ve already cost you money and catching problems before they cascade into your organization.
Types of Third Parties and Associated Risks
Not all third parties pose the same type or magnitude of risk. Here’s what security teams typically face:
Cybersecurity and InfoSec Risks
Cybersecurity risk is the potential for data breaches, ransomware infections, or unauthorized system access originating from a third party’s inadequate security controls. This is the most commonly cited third-party risk because vendors often hold sensitive data—customer records, intellectual property, financial information—or maintain direct network connectivity to your environment. A managed IT services provider with weak credential hygiene, for example, may allow attackers to pivot from the vendor’s environment into dozens of client networks.
Financial Dependencies
Financial risk is the exposure to vendor bankruptcy, sudden price increases, or payment processing failures that disrupt revenue collection or service delivery. A payment gateway provider experiencing liquidity problems may delay fund settlements, directly impacting an e-commerce company’s cash flow and ability to pay employees or restock inventory. Financial instability at a critical supplier can force emergency vendor transitions, cause contract disputes, or halt production lines entirely.
Operational Pitfalls
Operational risk is service outages, performance degradation, or delivery failures by third parties that interrupt business-critical workflows. Heavy reliance on a single SaaS platform, cloud infrastructure provider, or logistics partner creates what’s called concentration risk—if that vendor goes down, core business functions stop. An airline using a single crew-scheduling software vendor may be unable to assign pilots and flight attendants during an outage, forcing mass flight cancellations even though aircraft and runways are fully operational.
Compliance And Regulatory Challenges
Compliance risk is the legal and financial penalties your organization faces when a third party fails to meet data protection laws, industry standards, or contractual obligations. Under regulations like GDPR, HIPAA, and SEC cybersecurity disclosure rules, the hiring organization remains liable for third-party data handling and security failures. A healthcare provider whose billing contractor suffers a ransomware attack exposing patient records may face HIPAA fines, mandatory breach notifications, and class-action lawsuits—even if the provider’s own systems were never compromised.
Reputational Hazards
Reputational risk is brand damage, customer trust erosion, and negative media coverage resulting from a third party’s misconduct, data breach, or ethical violations. Consumers and regulators increasingly hold companies accountable for their vendors’ actions, especially in areas like data privacy, labor practices, and environmental standards. A retailer sourcing products from a supplier later exposed for unsafe working conditions may face boycotts and social media backlash—even though the retailer did not directly operate those facilities.
8 Notable Third-Party Risk Examples in 2026
The following examples are documented incidents from 2020-2026 involving household-name vendors and Fortune 500 enterprises. Each illustrates a different attack vector or failure mode that security teams face today.
1. Software Supply Chain Vulnerabilities
The SolarWinds Orion attack in 2020 demonstrated how nation-state actors compromised the vendor’s software build pipeline and injected malicious code into legitimate software updates. These updates were then distributed to approximately 18,000 customers including U.S. government agencies and Fortune 500 companies. The attack went undetected for months because customers trusted digitally signed updates from a reputable vendor—even trusted, widely deployed enterprise software can become a distribution channel for sophisticated attackers.
2. Widespread Vendor Patching Gaps
The Log4j “Log4Shell” vulnerability in 2021 created a critical flaw in a ubiquitous open-source logging library, generating exploitable weaknesses in thousands of commercial software products and cloud services. Many organizations discovered they were exposed not because they directly used Log4j, but because their SaaS vendors, security tools, or infrastructure platforms embedded the vulnerable library. A single upstream vulnerability created enterprise-wide exposure through multiple third-party products simultaneously.
3. Sub-Processor Data Breaches
The MOVEit Transfer zero-day exploitation by Cl0p ransomware group in 2023 enabled mass data theft from thousands of organizations—many of whom were not direct MOVEit customers but whose payroll processors, benefits administrators, or HR service providers used the platform. This incident highlighted fourth-party risk, which is exposure from your vendors’ vendors or sub-processors. Organizations face data breach liability even when the compromised system belongs to a vendor’s vendor, not a direct business partner.vendor’s vendor, not a direct business partner.
4. Critical Service Provider Downtime
The CrowdStrike Falcon sensor update incident in 2024 caused widespread Windows system crashes when a faulty software update from a dominant endpoint security vendor rendered millions of systems inoperable, requiring manual remediation at each affected machine. Delta Air Lines experienced an extended five-day recovery due to crew-scheduling system failures, resulting in over 5,400 flight cancellations and an estimated $350 million in lost revenue, passenger reimbursements, and regulatory penalties. Heavy reliance on a single vendor for mission-critical security or operational functions—concentration risk—can amplify the business impact of vendor failures.
5. Financial Instability at Key Vendors
Vendor financial distress or bankruptcy can force emergency transitions to alternative providers, disrupt contracted services, or leave organizations without technical support for critical systems. A mid-sized SaaS provider experiencing cash flow problems may suddenly announce end-of-service with 60 days’ notice, forcing enterprise customers to migrate data, retrain users, and reconfigure integrations under extreme time pressure. Financial due diligence—monitoring vendor revenue stability, debt levels, and going-concern indicators—matters as much as security assessments.
6. Embedded Fourth-Party Exposure
The Kaseya VSA ransomware attack in 2021 exploited a remote monitoring and management platform that primarily served managed service providers (MSPs). Attackers used this access to push ransomware through MSPs to thousands of downstream small and medium businesses with no direct relationship to Kaseya. This created a fourth-party breach affecting organizations multiple hops removed from the initially compromised vendor—security teams can’t just map direct vendors, they also have to understand critical sub-processors and service providers used by those vendors.
7. Credential Misuse By Outsourced Teams
The MGM Resorts and Caesars Entertainment breaches in 2023 began when attackers gained initial access by compromising VPN credentials from third-party IT support vendors, then used social engineering to bypass multi-factor authentication and impersonate legitimate help desk personnel. Outsourced IT support, help desk, and system administration functions create privileged access risk because external personnel hold credentials capable of making configuration changes or accessing sensitive data.
8. Compliance Failures By Global Contractors
The Capita data breach in 2023 resulted in a £14 million regulatory penalty and impacted over 6 million individuals. This incident involved a business process outsourcing provider handling sensitive personal data on behalf of UK public sector clients, and the breach exposed weaknesses in data handling, incident response, and contractual accountability. Under data protection regulations like GDPR, the data controller—your organization—remains legally liable for breaches at data processors, which are your vendors.
Common patterns emerge across these eight examples: attackers increasingly target vendors as a force-multiplier to reach many victims simultaneously, single points of failure in vendor ecosystems create cascading outages, and regulatory frameworks hold organizations accountable for third-party failures.

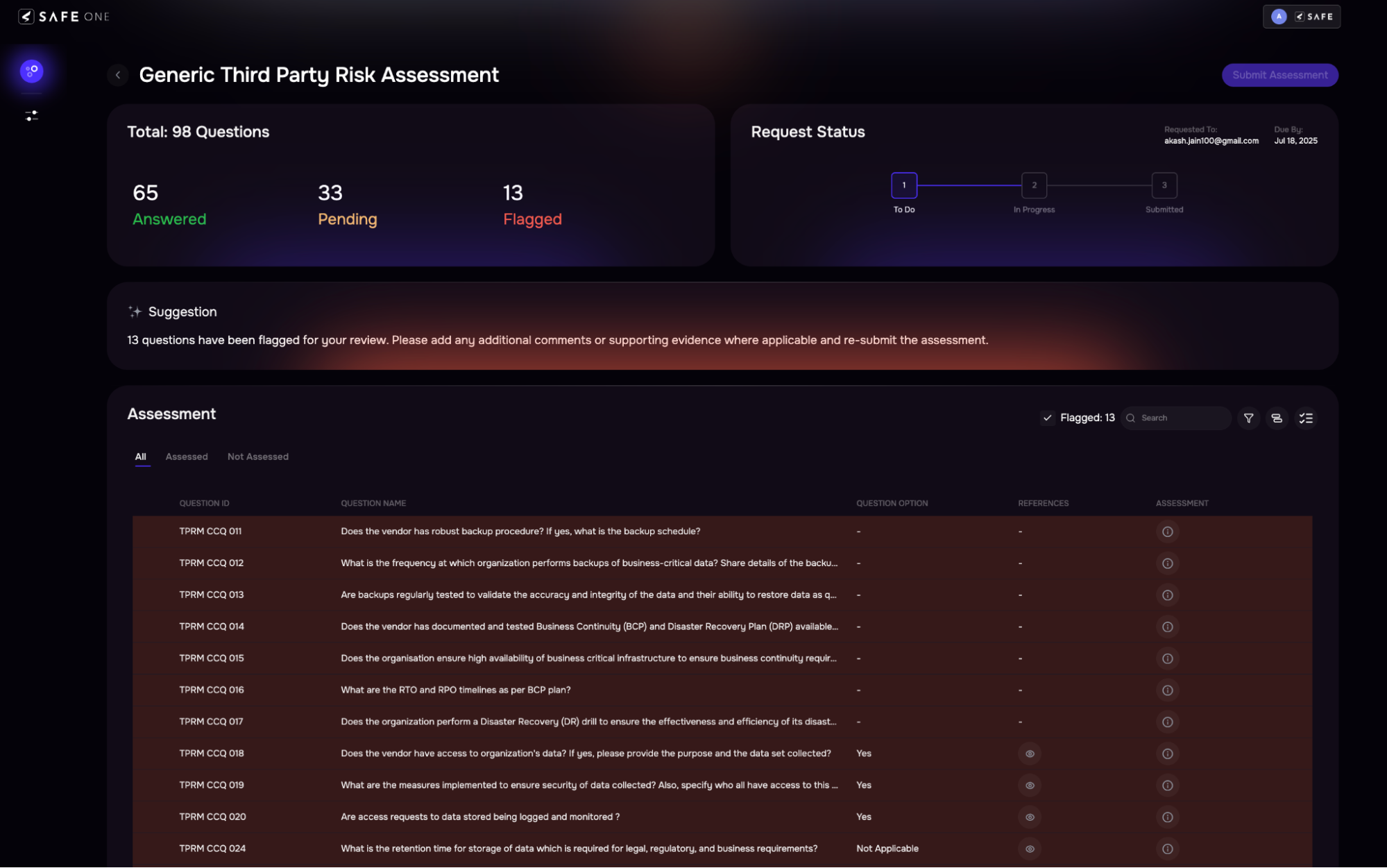
Tiering vendors by risk with the SAFE TPRM platform. Learn more about SAFE TPRM
How to Identify Critical Third-Party Data Exposures
Identifying third-party data exposures starts with answering three questions: Which vendors have access to what data? Where is that data stored and processed? What security controls protect it?
Start by creating a vendor inventory—a comprehensive list of all third parties with system access, data processing roles, or integration points. Many organizations discover they have 3-5 times more vendor relationships than initially estimated because business units procure SaaS tools, professional services, and cloud resources without centralized IT approval, a phenomenon called shadow IT. Then conduct data mapping by documenting what categories of data—customer PII, payment card information, health records, intellectual property—each vendor collects, processes, stores, or transmits.
Next, perform access audits to document which vendor personnel, API keys, service accounts, or integration credentials have privileged access to your production environment, databases, or admin consoles. Excessive vendor permissions—granting broader access than necessary to perform contracted services—expand the attack surface if vendor credentials are compromised. Finally, assess control coverage by reviewing vendor security questionnaires, SOC 2 reports, ISO 27001 certifications, and penetration test results.
When prioritizing which vendors to scrutinize most closely, consider:
- Privileged access: Does the vendor have admin rights, database access, or the ability to push code or configuration changes to production?
- Data sensitivity: Does the vendor process regulated data (PII, PHI, payment card data) that triggers mandatory breach notification and penalties?
- Concentration risk: Are critical business functions dependent on a single vendor with no failover or alternative provider?
- Fourth-party dependencies: Does the vendor rely on sub-processors or cloud infrastructure providers that introduce additional exposure?
Managing Third Party Risk with Continuous Monitoring
Traditional TPRM relies on annual vendor assessments—security questionnaires, document reviews, and compliance audits conducted once per year or at contract renewal. This approach creates a visibility gap, which is the period between assessments when vendor security posture, financial health, or threat exposure may degrade without detection.
Continuous monitoring uses automated data collection, threat intelligence feeds, and external security ratings to track vendor risk in real time. External attack surface scanning continuously scans vendor domains, IP ranges, and cloud environments for exposed databases, unpatched vulnerabilities, misconfigured S3 buckets, or leaked credentials on the dark web. Threat intelligence integration subscribes to breach notification feeds, vulnerability databases (CVE, NVD), and ransomware victim trackers to receive alerts when vendors appear in incident reports or ransom leak sites.
Continuous monitoring enables event-driven reassessment—triggering an immediate vendor review when risk indicators spike—rather than waiting for the next scheduled audit cycle. If a vendor appears on a ransomware leak site or experiences a publicized breach, the TPRM team can immediately escalate to incident response, activate contract breach clauses, or implement compensating controls.
Modern TPRM platforms use Agentic AI—autonomous AI agents that perform specific tasks without human intervention—to automate data ingestion from hundreds of vendor security tools, correlate findings across multiple risk domains, and generate prioritized remediation workflows. Organizations using SAFE TPRM can onboard, assess, and continuously monitor vendors at scale without adding headcount, and prioritize vendors based on actual cybersecurity risk and potential financial loss rather than static ratings.
Best Practices to Assess 3rd-Party Risk at Scale
Effective TPRM programs balance thoroughness with efficiency—conducting deep due diligence on high-risk vendors while streamlining assessments for lower-risk relationships.
1. Automate Vendor Onboarding
Manual vendor onboarding—emailing security questionnaires, chasing responses, manually reviewing documents—creates bottlenecks that delay procurement and frustrate business stakeholders. Automated onboarding workflowsManual vendor onboarding—emailing security questionnaires, chasing responses, manually reviewing documents—creates bottlenecks that delay procurement and frustrate business stakeholders. Automated onboarding workflows use software-driven processes that collect vendor information, trigger risk assessments, and route approvals based on predefined rules, reducing time-to-approval from weeks to days. When a new vendor is proposed, the TPRM platform automatically sends a risk assessment questionnaire, requests compliance documentation (SOC 2, ISO 27001, cyber insurance certificates), and performs external security scans.
2. Conduct Periodic Due Diligence
Vendor risk is not static—security controls degrade, financial conditions change, and new vulnerabilities emerge. A tiered reassessment schedule works well: critical vendors (those with privileged access to production systems or processing highly sensitive data) receive quarterly reassessment; high-risk vendors (those with moderate access or data exposure) get semi-annual reassessment; low-risk vendors (limited access, non-sensitive data) undergo annual reassessment. Continuous monitoring supplements scheduled assessments by providing real-time alerts for security incidents, compliance lapses, or financial distress between formal review cycles.
3. Tier Vendors By Actual Risk Exposure
Not all vendors pose equal risk, and treating every vendor relationship the same wastes resources on low-impact assessments while under-investing in critical vendors. Risk-based tiering categorizes vendors by potential financial loss and likelihood of incident, allowing security teams to allocate due diligence effort proportionally.
Impact measures potential financial loss if the vendor experiences a breach, outage, or compliance failure, considering volume and sensitivity of data the vendor processes, criticality of vendor services to business operations, and contractual liability and regulatory penalties triggered by vendor failures. Likelihood assesses probability that the vendor will experience a security incident or operational failure, factoring in external security ratings and attack surface exposure, history of breaches or security incidents, financial stability and business continuity maturity, and compliance certification status.
| Impact | High Likelihood | Low Likelihood |
| High Impact | Critical Risk: Quarterly assessments, on-site audits, continuous monitoring, contractual security requirements | Elevated Risk: Semi-annual assessments, external security scans, incident response planning |
| Low Impact | Moderate Risk: Annual assessments, automated monitoring, standard contract terms | Low Risk: Lightweight questionnaire, auto-renewal, periodic spot checks |
4. Measure Financial Impact Of Control Gaps
Traditional TPRM programs report vendor risk in qualitative terms (“high,” “medium,” “low”) that don’t resonate with business executives or justify budget requests. Cyber risk quantification translates security findings into expected financial loss using probabilistic models like FAIR, enabling CISOs to communicate third-party risk in business language. Cyber risk quantification translates security findings into expected financial loss using probabilistic models like FAIR, enabling CISOs to communicate third-party risk in business language.
For each critical vendor, calculate the expected annual loss—probability of an incident multiplied by estimated financial impact—using FAIR methodology based on threat event frequency (how often do vendors in this industry experience breaches or outages?), vulnerability (what is the likelihood that an attack or failure at this vendor will succeed given their current security controls?), and loss magnitude (if an incident occurs, what are the estimated costs including data breach response, regulatory fines, business interruption, customer churn, and legal settlements?).
SAFE CRQ measures enterprise-wide cyber risk in dollars and cents using FAIR standards, automatically aggregates data from over 100 security tools, and continuously monitors exposure—enabling CISOs to prioritize third-party risk investments based on expected risk reduction and create board-ready reports aligned with SEC and NYDFS regulatory frameworks.
Key Steps to Mitigate Each Type of Third-Party Risk
Mitigation strategies address the specific failure modes illustrated in the eight examples: supply chain attacks, widespread vulnerabilities, credential compromise, service outages, financial instability, fourth-party exposure, and compliance failures.
1. Contractual Safeguards and SLAs
Contracts are the foundation of third-party risk management—they define security obligations, liability allocation, breach notification timelines, audit rights, and termination conditions. Security exhibit clauses (contract addenda specifying mandatory security controls, incident response procedures, and compliance requirements) make vendor security commitments legally enforceable.
Include these provisions:
- Mandatory security controls: Require multi-factor authentication, encryption of data at rest and in transit, annual penetration testing, and SOC 2 Type II certification
- Breach notification: Require vendors to notify you within 24-48 hours of discovering a security incident affecting your data or systems
- Audit rights: Reserve the right to conduct on-site security audits, review vendor sub-processor agreements, and access incident response documentation
- Liability caps and cyber insurance: Require vendors to maintain cyber liability insurance with coverage limits proportional to potential breach costs
- Termination for cause: Include provisions allowing immediate contract termination if the vendor experiences a material security breach or loses required compliance certifications
Service Level Agreements (SLAs)—contractual commitments specifying uptime guarantees, performance benchmarks, and financial penalties for non-compliance—mitigate operational risk by ensuring vendors maintain business continuity standards.
2. Real-Time Threat Intelligence
Security teams benefit from early warning when vendors experience breaches, become ransomware targets, or appear in vulnerability disclosures. Threat intelligence integrationSecurity teams benefit from early warning when vendors experience breaches, become ransomware targets, or appear in vulnerability disclosures. Threat intelligence integration consumes external data feeds about vendor security incidents, exposed credentials, and emerging threats, enabling proactive risk response. Key intelligence sources include breach notification databases (services that aggregate data breach disclosures, SEC 8-K filings, and regulatory enforcement actions), dark web monitoring (scans of criminal forums, ransomware leak sites, and credential marketplaces), vulnerability feeds (CVE databases, vendor security advisories, and exploit availability trackers), and security ratings services (third-party platforms that continuously scan vendor attack surfaces).
3. Incident Response Collaboration
Third-party breaches require coordinated response between your security team, the vendor’s incident response team, legal counsel, and potentially cyber insurers and regulators. Joint incident response planning involves pre-negotiated procedures, communication channels, and decision frameworks for managing vendor-originated incidents, reducing confusion and delays during active breaches. Organizations with mature TPRM programs conduct tabletop exercises—simulated incident response drills—with critical vendors to test communication channels and decision-making processes before real incidents occur.
4. Regular Compliance Audits
Compliance risk requires ongoing verification that vendors maintain required certifications, adhere to contractual security obligations, and implement promised controls. Compliance audits involve structured reviews of vendor policies, procedures, and technical controls against regulatory standards or contractual requirements, providing independent validation beyond vendor self-assessments. Audit findings trigger formal remediation plans with defined timelines, executive accountability, and follow-up verification.
Frequently Asked Questions a bout Third-Party Risk
What Is the Difference Between Third-Party Risk and Fourth-Party Risk?
Third-party risk originates from vendors you directly contract with (software providers, cloud platforms, professional services firms), while fourth-party risk comes from sub-processors, suppliers, or service providers that your vendors depend on but you have no direct contractual relationship with. Fourth-party breaches can still impact your organization because data or services flow through indirect dependencies, as seen in the MOVEit and Kaseya incidents.
How Does Continuous Monitoring Reduce Manual TPRM Workloads?
Continuous monitoring uses automated external scans, threat intelligence feeds, and API integrations to track vendor security posture, compliance status, and breach disclosures in real time, eliminating the labor of manually chasing vendor questionnaire responses, reviewing documents, or scheduling annual audits for every vendor relationship. AI-driven platforms can autonomously assess hundreds or thousands of vendors simultaneously and alert teams only when risk thresholds are exceeded or incidents occur.
What Types of Third Parties Present the Highest Cybersecurity Risk?
Software vendors with privileged access to production systems, cloud infrastructure providers hosting sensitive data, managed IT service providers with administrative credentials, and payment processors handling financial transactions consistently present the highest cybersecurity risk because compromises at these vendors enable attackers to access multiple customers simultaneously or exfiltrate large volumes of regulated data.
How Often Should Vendor Risk Assessments Be Updated?
Critical vendors with privileged access or sensitive data processing receive quarterly reassessment, high-risk vendors get semi-annual reassessment, and low-risk vendors undergo annual reassessment—but continuous monitoring supplements scheduled assessments by providing real-time alerts for security incidents, compliance lapses, or financial distress between formal review cycles. Event-driven reassessments (triggered by breach disclosures, failed audits, or major vendor changes) are equally important as scheduled reviews.