
By Resha Chheda
Another RSAC done, and like every year, there was a lot of noise, big claims, and booths trying to say something slightly different but mostly sounding the same.
But when you step back from the floor, the sessions, and the conversations, a few patterns become hard to ignore. These weren’t just trends people were talking about. These are gaps people are actually struggling with.
Here’s what stood out and what it really means going forward.
1. Everyone Is Talking about AI, but Very Few Are Showing Real Decisions
AI was everywhere this year. It showed up in keynotes, product demos, and almost every booth on the floor. But if you looked closely, most of it still felt like assistance rather than action.
A lot of tools are getting better at summarizing information, generating insights, and pointing teams in the right direction. But very few are actually helping teams make decisions end to end or move those decisions forward without manual effort.
There is still a heavy reliance on humans to interpret, prioritize, and execute. You can see the shift from tools that inform to systems that act. From dashboards and copilots to workflows that actually drive outcomes.
This is exactly where both CTEM and TPRM need to go. Security teams do not need more information surfaced to them. They need fewer decisions sitting in queues waiting to be made.
2. Exposure Is Not the Problem Any More. Making Sense of It Is.
If there was one thing everyone seemed to agree on, it is that visibility is no longer the bottleneck.
Most organizations already have more data than they know what to do with. Between cloud environments, identity systems, endpoints, and third-party integrations, the volume of signals has exploded.
The real challenge is not collecting data. It is connecting it in a way that actually reflects risk.
Teams are still asking very basic questions that are surprisingly hard to answer. Which exposures actually matter to the business? Which vulnerabilities should be fixed first? Which third parties introduce meaningful risk versus theoretical risk?
This is where CTEM is starting to resonate more. Not as another layer of scanning or aggregation, but as a way to bring context, prioritization, and defensibility into how teams decide what to do next.
The same issue shows up in third-party risk. Many programs are still built around compliance and questionnaires, while attackers are taking advantage of real exposure paths that sit outside those processes.
That gap is becoming more visible and harder to justify.
3. Third-Party Risk Is Becoming a Core Part of Security Strategy
This year, third-party risk was not confined to TPRM sessions or niche discussions. It showed up across keynotes, hallway conversations, and broader security discussions.
Recent breaches have made it clear that risk does not stay contained within your own environment. It moves through vendors, partners, and integrations in ways that are often not fully understood.
There is a growing realization that an approved vendor does not necessarily mean a secure vendor, and that point-in-time assessments are not enough to keep up with how quickly risk changes.
What is emerging is a shift from periodic reviews to continuous monitoring, and more importantly, toward real-time decision-making.
The question is no longer whether a vendor passed a questionnaire six months ago. The question is what level of risk that vendor introduces right now, given their current exposure and your business dependency on them.
That is a fundamentally different problem to solve, and it requires a very different approach than traditional TPRM programs.
4. The Scaling Challenge Is Breaking Traditional Security Models
One of the more honest themes that came up repeatedly in conversations was how stretched security teams are.
There is no shortage of tools, alerts, and findings. What is missing is the capacity to process and act on all of it.
At the same time, there is very little expectation that teams will simply hire their way out of this problem. Budgets are tight, and adding headcount does not scale with the growth of exposure.
As a result, the conversation is shifting from how to do more to what should no longer be done manually.
This is where automation starts to move from being helpful to being necessary. Not just automating isolated tasks, but driving end-to-end workflows.
For CTEM and TPRM, this shows up as automating assessments, coordinating follow-ups, prioritizing remediation, and ensuring that actions actually get completed rather than getting lost in backlogs.
5. The Winners Will Connect Risk across Domains, not Isolate it
One of the biggest structural gaps that still exists is how fragmented risk management is across organizations.
Exposure management lives in one system. Third-party risk lives in another. Risk quantification is often handled separately. Different teams own each piece, and each operates with its own data and language.
But in reality, risk does not exist in silos.
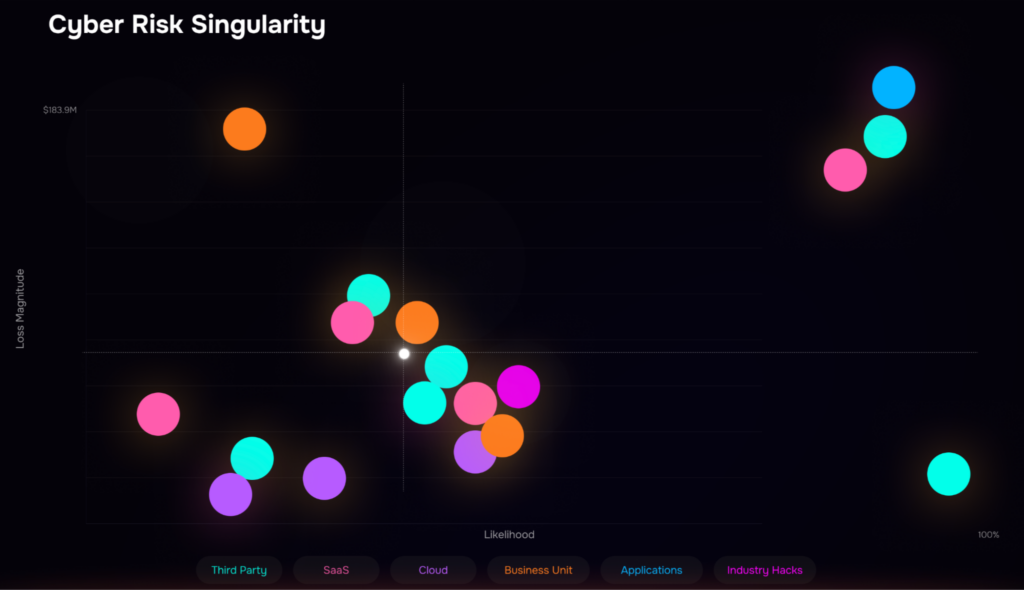
A vulnerable system combined with a third-party integration and tied to a critical business process is how real incidents happen.
What became clear at RSAC is that the next wave of platforms will not win by going deeper in a single category alone. They will win by connecting these domains into a single, continuous view of risk.
From exposure to business impact to action.
Not as separate workflows, but as one system that reflects how risk actually behaves.
Conclusion
RSAC this year felt like a turning point, not because of any single launch, but because the industry is starting to align on what actually needs to change.
Security teams are not short on tools or data. They are short on clarity and on the ability to consistently act on what matters.
That is where agentic AI starts to become real. Not as another layer of intelligence, but as a way to actually drive decisions and carry work forward across workflows.
The shift is moving from fragmented visibility to connected, agentic decision-making. From manual coordination to systems that can continuously assess, prioritize, and act.
That is exactly the problem we have been focused on solving across CTEM and TPRM. Connecting exposure, third-party risk, and business impact into one system, and using agentic workflows to move from insight to action.
If you are rethinking how your team prioritizes and manages risk, it is worth seeing how this works in practice.
See CRQ, TPRM and CTEM in action: Schedule your SAFE demo now.


