Recognize the attack patterns shaping today’s threat landscape

By SAFE Threat Research Team
This week’s vulnerabilities highlight a consistent and concerning pattern: unauthenticated access, internet-facing systems, and active exploitation are converging. Many of these flaws are not just theoretical—they are already being used by ransomware groups, nation-state actors, and opportunistic attackers.
Below are six of the most significant CVE clusters from this week’s data, with added context on why they matter operationally.
#1 Cisco Secure Firewall Management Center RCE (Zero-Day)
CVE-2026-20131
An insecure deserialization vulnerability in Cisco Secure Firewall Management Center allows remote unauthenticated attackers to execute arbitrary code via crafted HTTP requests. Successful exploitation results in full system compromise with root-level privileges.
This vulnerability is a zero-day actively exploited by the Interlock ransomware group.
Why it matters
This is a high-risk scenario combining multiple dangerous characteristics:
- No authentication required
- No user interaction needed
- Targets internet-facing firewall management systems
In practical terms, this means attackers can:
- Take over firewall infrastructure
- Establish persistence
- Move laterally across the network
This is not just an endpoint issue—it’s a control-plane compromise, which can expose the entire enterprise.
Trend illustrated
Attackers are prioritizing security infrastructure itself (firewalls, management consoles) as a high-leverage entry point.
#2 Microsoft SharePoint Remote Code Execution
CVE-2026-20963
A deserialization vulnerability in Microsoft SharePoint allows attackers to execute arbitrary code by sending crafted data to vulnerable servers.
The flaw is actively exploited in the wild and is network exploitable with no user interaction required.
Why it matters
SharePoint is widely deployed and often internet-facing. Successful exploitation can lead to:
- Full server compromise
- Unauthorized command execution
- Rapid lateral movement across enterprise environments
Because SharePoint often integrates deeply with identity systems and internal workflows, compromise here can quickly expand beyond a single system.
Trend illustrated
Attackers continue to target business-critical collaboration platforms that provide both access and trust inside the enterprise.
#3 Wing FTP Server Exploit Chain (RCE + Information Disclosure)
CVE-2025-47812
CVE-2025-47813
This cluster combines:
- A remote code execution vulnerability
- An information disclosure flaw exposing internal server paths
Together, they enable attackers to gain an initial foothold and then expand access using exposed system details.
These vulnerabilities are actively exploited and listed in the Known Exploited Vulnerabilities (KEV) catalog.
Why it matters
This is a clear example of chained exploitation:
- RCE provides initial access
- Information disclosure enables deeper compromise
This combination allows attackers to:
- Execute arbitrary code
- Map internal environments
- Establish persistence and move laterally
Trend illustrated
Attackers are increasingly combining vulnerabilities into multi-stage attack chains, rather than relying on a single exploit.
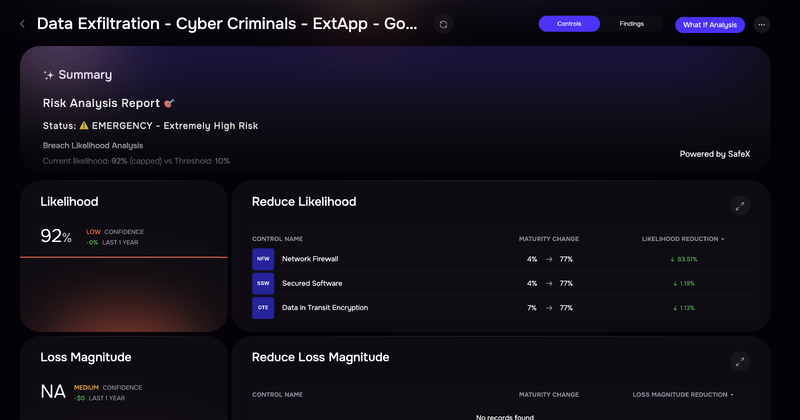
The SAFE One platform displays risk scenarios grouped by threat actors
#4 Zimbra Collaboration Suite XSS (Phishing-Driven Exploitation)
CVE-2025-66376
A stored cross-site scripting (XSS) vulnerability in Zimbra Collaboration Suite allows attackers to inject malicious content via crafted HTML emails.
This vulnerability is being actively exploited in targeted phishing campaigns (Operation GhostMail) attributed to APT28.
Why it matters
This attack blends social engineering with technical exploitation:
- A single email triggers an in-browser payload
- Enables credential theft and session hijacking
- Allows persistent access via app passwords and API abuse
Unlike traditional exploits, this one leverages trusted user workflows (email) to bypass defenses.
Trend illustrated
The continued convergence of phishing + application-layer vulnerabilities to increase attack success rates.
#5 Microsoft SQL Server Privilege Escalation
CVE-2026-21262
An elevation-of-privilege vulnerability in Microsoft SQL Server allows authenticated attackers to gain SQLAdmin privileges due to improper access control in stored procedures.
The vulnerability is actively exploited, requires low privileges, and is network accessible.
Why it matters
While this vulnerability requires initial access, it becomes extremely dangerous post-compromise:
- Attackers can escalate to full database control
- Modify or exfiltrate sensitive data
- Create new privileged accounts
Given how central SQL Server is to enterprise operations, this can quickly lead to business-critical impact.
Trend illustrated
Attackers are focusing not just on entry—but on privilege escalation inside core data systems.
#6 Google Chrome Zero-Day Memory Corruption
CVE-2026-3909
CVE-2026-3910
These vulnerabilities affect Chrome’s:
- Skia graphics library
- V8 JavaScript/WebAssembly engine
They allow attackers to execute arbitrary code via malicious web content and are actively exploited zero-days.
Why it matters
This is a classic but still highly effective attack vector:
- Targets end users through normal browsing behavior
- Requires minimal interaction
- Serves as an entry point for multi-stage exploit chains
Once the browser is compromised, attackers can pivot to:
- Endpoint compromise
- Credential theft
- Internal network access
Trend illustrated
Browsers remain one of the most reliable initial access vectors, especially when paired with zero-days.
Key Patterns Across This Week’s Vulnerabilities
Several consistent themes emerge across these six clusters:
1. Unauthenticated + Internet-Facing = Immediate Risk
Multiple vulnerabilities require no authentication and no user interaction, making them highly scalable and easy to exploit.
2. Active Exploitation Is the Baseline
Every vulnerability listed is already being exploited. The question is no longer if exploitation will occur—but how widely and how quickly.
3. Attackers Are Targeting High-Leverage Systems
Firewall managers, SharePoint, SQL Server—these are not random targets. They are systems that:
- Control infrastructure
- Store sensitive data
- Enable lateral movement
4. Chaining and Post-Exploitation Are Effective Tactics
Attackers are increasingly combining:
- Initial access (RCE)
- Internal discovery (info disclosure)
- Privilege escalation
This reflects a shift toward end-to-end attack path optimization.
What This Means for Security Teams
This week’s vulnerabilities reinforce a practical shift in how risk should be managed:
The most dangerous vulnerabilities are those that combine:
- Network exploitability
- Low or no privilege requirements
- High-impact systems
Security teams should prioritize:
- Internet-facing assets tied to these CVEs
- Systems with control-plane or data-plane importance
- Vulnerabilities already observed in active campaigns
In short, the focus should not be on volume—but on which vulnerabilities meaningfully increase the probability and impact of breach.
That’s where real risk reduction happens.
SAFE brings order to the thousands of CVEs by moving away from “technical severity” (which is static) and toward “contextual risk” (which is dynamic). SAFE uses a 6-step automated engine to filter out the noise and find the small fraction of vulnerabilities that actually pose a financial threat to your business. Contact us to see a demo.