Identify the patterns among the most dangerous exposures

By SAFE Threat Research Team
This week’s vulnerabilities reinforce a clear shift in attacker strategy: compromise the software supply chain, exploit internet-facing applications, and chain vulnerabilities to achieve full system control. All of the issues below are actively exploited, and several are being used in coordinated campaigns by ransomware groups and nation-state actors.
As with prior weeks, the signal is not just severity—it’s how directly these vulnerabilities translate into enterprise-wide impact.
#1 Supply Chain Compromise: Aqua Security Trivy / GitHub Actions
CVE-2026-33634
This issue represents a software supply chain compromise affecting Aqua Security Trivy and related GitHub Actions (trivy-action, setup-trivy). A threat actor used compromised credentials to publish a malicious release, embedding credential-stealing code into distributed components.
The campaign is actively exploited by TeamPCP / CipherForce ransomware operators, delivering infostealer malware (“TeamPCP Cloud stealer”) into developer and CI/CD environments.
Why it matters
This is not a traditional vulnerability—it’s a trusted software compromise. That changes the risk profile entirely:
- Malicious code is delivered through legitimate update channels
- Impacts developers, pipelines, and cloud-connected environments
- Enables credential harvesting at scale
Downstream impact includes compromise of dependent tools (Trivy, Checkmarx, LiteLLM) and follow-on ransomware operations.
Trend illustrated
Attackers are moving upstream—targeting software supply chains and CI/CD pipelines to maximize downstream blast radius.
#2 Apple iOS / WebKit Full-Chain Exploit (DarkSword)
Multiple CVEs
(CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, CVE-2025-43520)
This cluster includes multiple memory corruption, use-after-free, and improper memory handling vulnerabilities across iOS and WebKit. These flaws can be chained to achieve:
- Remote code execution
- Sandbox escape
- Kernel-level compromise
The vulnerabilities are actively exploited as part of the DarkSword full-chain exploit, used by multiple threat actors (UNC6748, PARS Defense, UNC6353).
Why it matters
This is a complete device takeover chain, not a single bug. It enables:
- Safari drive-by compromise
- Full device control
- Deployment of spyware payloads (GHOSTKNIFE, GHOSTSABER, GHOSTBLADE)
Trend illustrated
The continued rise of multi-stage exploit chains targeting mobile platforms, combining multiple vulnerabilities to bypass layered defenses.
#3 Laravel Livewire Remote Code Execution (Iranian APT Activity)
CVE-2025-54068
A code injection vulnerability in Laravel Livewire allows attackers to execute arbitrary commands due to improper handling of user-supplied input.
The vulnerability is:
- Network exploitable
- Requires no privileges
- Requires no user interaction (CVSS 9.2)
It is actively exploited by MuddyWater (GreenGolf) linked to Iranian threat actors in campaigns targeting diplomatic, energy, and financial sectors.
Why it matters
This is a classic initial access vulnerability:
- Internet-facing application layer
- Low complexity exploitation
- Direct path to command execution
Once exploited, attackers can establish persistence and pivot deeper into the environment.
Trend illustrated
Nation-state actors continue to rely on straightforward, high-reliability exploits for initial access—favoring consistency over complexity.
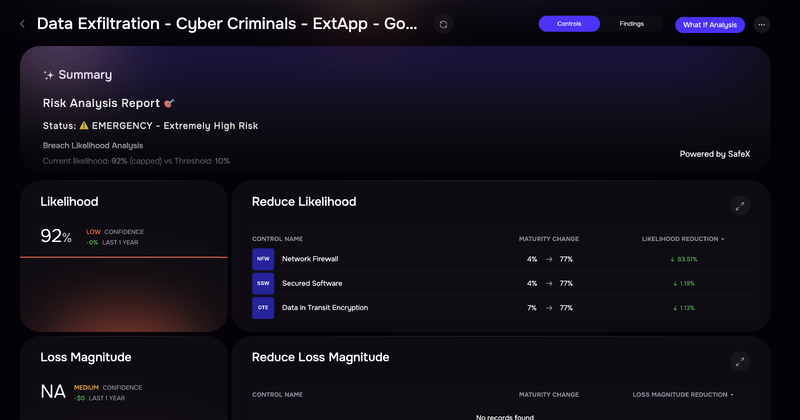
The SAFE One platform displays risk scenarios grouped by threat actors
#4 Craft CMS Unauthenticated Remote Code Execution
CVE-2025-32432
Craft CMS (flexible, user-friendly CMS for creating custom digital experiences on the web and beyond) is vulnerable to remote code execution. This is a high-impact remote code execution via a low-complexity attack vector, enabling attackers to execute arbitrary code on affected systems.
The vulnerability is actively exploited, with exploit kits already available.
Why it matters
This vulnerability checks several high-risk boxes:
- Unauthenticated exploitation
- Targets internet-facing CMS platforms
- Easy to weaponize and scale
Attackers can use this to:
- Gain immediate access to web servers
- Deploy webshells
- Use compromised systems as entry points into internal networks
Trend illustrated
Content management systems remain a persistent weak point, especially when vulnerabilities allow unauthenticated remote access at scale.
#5 Quest KACE SMA Authentication Bypass
CVE-2025-32975
An authentication bypass vulnerability in Quest KACE Systems Management Appliance for endpoints allows attackers to bypass SSO authentication and gain administrative access.
The vulnerability is actively exploited in the wild.
Why it matters
KACE SMA is a systems management platform, which makes this particularly dangerous:
- Attackers can authenticate as legitimate users
- Gain administrative control over managed systems
- Potentially push malicious updates or commands across endpoints
This is effectively a control-plane compromise, similar to other management platform vulnerabilities.
Trend illustrated
Attackers are increasingly targeting IT management systems to gain broad control over enterprise environments.
#6 F5 BIG-IP APM Remote Code Execution (KEV-Listed)
CVE-2025-53521
This vulnerability affects F5 BIG-IP Access Policy Manager, allowing remote code execution via specially crafted traffic sent to a virtual server with an access policy.
Key characteristics:
- Network exploitable
- No privileges required
- No user interaction (CVSS 9.8)
- Added to CISA KEV catalog
Originally misclassified as a denial-of-service issue, it has since been reclassified as RCE, with confirmed exploitation, webshell activity, and widespread scanning.
Why it matters
BIG-IP devices are often internet-facing and security-critical. Exploitation allows:
- Arbitrary code execution
- Deployment of webshells
- Persistent access to sensitive infrastructure
Because of their role in access management, compromise here can expose large portions of the enterprise.
Trend illustrated
Misclassification delays and rapid reclassification highlight how quickly vulnerabilities can evolve from underestimated to critical once exploitation begins.
Key Patterns Across This Week’s Vulnerabilities
Several themes stand out:
1. Supply Chain Attacks Are Escalating
The Trivy compromise shows attackers targeting trusted developer tooling, expanding impact far beyond a single organization.
2. Unauthenticated RCE Remains the Highest Risk Category
Multiple vulnerabilities allow remote exploitation with no credentials, making them ideal for large-scale campaigns.
3. Control-Plane Systems Are Prime Targets
From KACE to BIG-IP, attackers are targeting systems that provide centralized control over infrastructure and users.
4. Exploit Chains and Campaign Context Matter
The iOS DarkSword chain and MuddyWater campaigns show that vulnerabilities are increasingly part of coordinated operations, not isolated exploits.
What This Means for Security Teams
This week’s vulnerabilities reinforce a consistent operational takeaway:
The most dangerous exposures are those that combine:
- Internet accessibility
- No authentication requirements
- High-privilege impact
Security teams should prioritize:
- External-facing systems tied to these CVEs
- Developer and CI/CD environments (for supply chain risk)
- Management and access control platforms
As vulnerability volume continues to grow, the differentiator is not how many issues you patch—but how effectively you identify the small subset that materially drives enterprise risk.
That’s where meaningful risk reduction happens.
———–
SAFE brings order to the thousands of CVEs by moving away from “technical severity” (which is static) and toward “contextual risk” (which is dynamic). SAFE uses a 6-step automated engine to filter out the noise and find the small fraction of vulnerabilities that actually pose a financial threat to your business. Contact us to see a demo.


