Recognize the attack patterns shaping today’s threat landscape
By SAFE Threat Research Team
In the past few days, several high-impact vulnerabilities have emerged across enterprise infrastructure, browsers, mobile devices, and widely deployed management platforms. Individually, each issue is serious. Taken together, they illustrate several important patterns shaping today’s threat landscape: attackers targeting control-plane infrastructure, weaponizing browser and mobile exploits, and prioritizing unauthenticated remote access paths that can rapidly scale across organizations.
Below are six notable vulnerability groupings recently reported, ranked roughly by potential enterprise impact. Each highlights a different dimension of modern cyber risk.
#1 Cisco Catalyst SD-WAN Manager Authentication Bypass
CVE-2026-20127
CVE-2026-20122
CVE-2026-20128
These vulnerabilities affect Cisco Catalyst SD-WAN Manager, a platform used by many enterprises to centrally manage wide-area networks.
The flaws allow authentication bypass and access control failures, enabling remote attackers to gain administrative access to network control infrastructure. One of the vulnerabilities is a zero-day that has already been exploited in the wild by threat actor UAT-8616, which used the weakness to obtain persistent administrative access.
Public proof-of-concept exploit code is already circulating, which significantly increases the risk of broader exploitation.
Why it matters
This vulnerability targets the network control plane, which is one of the most sensitive parts of enterprise infrastructure. If attackers gain access to SD-WAN management systems, they can potentially:
- Manipulate network routing
- Intercept traffic
- Disable security controls
- Establish persistent backdoor access
In other words, compromise of this platform could give an attacker visibility and control across an organization’s network environment.
Trend illustrated
Attackers are increasingly targeting network orchestration platforms and control infrastructure, recognizing that compromise there provides broad leverage across enterprise environments.
#2 Qualcomm Chipset Zero-Day in Android Devices
CVE-2026-21385
This vulnerability affects Qualcomm chipsets used in Android devices, allowing attackers to exploit a memory corruption flaw that enables arbitrary code execution or privilege escalation.
The issue is already being exploited in targeted attacks.
Why it matters
Unlike software vulnerabilities that affect a single application, chipset flaws impact millions of devices at the hardware level. Because Qualcomm processors power a large portion of the Android ecosystem, the attack surface is extremely large.
Successful exploitation can allow attackers to:
- Escalate privileges within the operating system
- Execute arbitrary code
- Bypass security protections on the device
These vulnerabilities are often used in mobile surveillance or advanced espionage campaigns.
Trend illustrated
Mobile devices continue to be a major intelligence target. Hardware and firmware vulnerabilities are increasingly exploited because they can bypass many traditional software security controls.
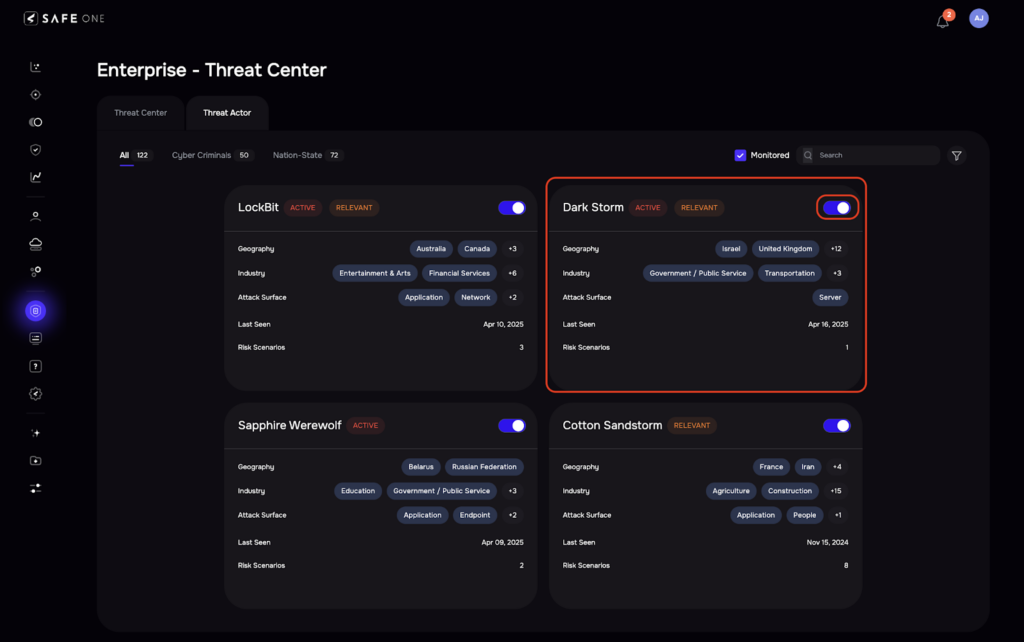
The SAFE platform Enterprise Threat Center tracks over 100 threat actors.
#3 Apple iOS WebKit and Kernel Exploit Chain
CVE-2022-48503
CVE-2024-23222
CVE-2023-32409
CVE-2020-27932
CVE-2020-27950
CVE-2023-32434
CVE-2023-38606
CVE-2024-23225
CVE-2024-23296
This cluster of vulnerabilities involves multiple WebKit and iOS kernel flaws chained together to achieve sandbox escape and full device compromise.
These vulnerabilities are reportedly part of the Coruna exploit kit, a spyware-grade toolkit used by several threat actors including:
- A commercial spyware vendor customer
- A Russian espionage group
- A financially motivated Chinese threat actor
Why it matters
Modern mobile operating systems rely heavily on sandboxing to isolate apps and prevent full device compromise. Exploit chains like this combine several vulnerabilities to bypass those protections.
Once attackers break out of the sandbox, they can potentially:
- Install spyware
- Monitor communications
- Access sensitive data
- Track user activity
These types of exploit chains are typically seen in nation-state or high-end surveillance operations.
Trend illustrated
High-value mobile targets continue to attract multi-stage exploit chains, where attackers combine several vulnerabilities to bypass layered defenses.
Related blog post: Understand the Risk-based Scoring of SAFE’s Findings Prioritization
#4 Google Chrome Rendering Engine Zero-Day
CVE-2026-2441
This vulnerability is a use-after-free flaw in the Chrome rendering engine that allows attackers to achieve remote code execution when a user visits a malicious webpage.
The vulnerability is actively exploited, and the exploit details are publicly available.
Why it matters
Browsers remain one of the most exposed components in enterprise environments. Every employee interacts with the web daily, making browser vulnerabilities highly attractive to attackers.
If successfully exploited, this flaw could allow attackers to:
- Execute code on a victim’s machine
- Install malware
- Establish footholds inside corporate environments
Because exploitation can occur simply by visiting a malicious webpage, large-scale attacks are possible.
Trend illustrated
Browser vulnerabilities remain one of the most reliable initial access vectors in cyber attacks.
#5 VMware vCenter Server Template Injection
CVE-2021-22054
This vulnerability affects VMware vCenter Server, the central management platform used to administer virtualized infrastructure in many enterprise data centers.
The flaw is a server-side template injection vulnerability that can allow remote attackers to achieve remote code execution or administrative access.
The vulnerability is known to be actively exploited, particularly against internet-exposed vCenter instances.
Why it matters
vCenter servers effectively control large portions of enterprise infrastructure. Compromise of vCenter can allow attackers to:
- Access virtual machines
- Deploy malicious workloads
- Pivot deeper into the network
Security researchers continue to observe attackers scanning for exposed vCenter servers due to the high return on investment when exploitation succeeds.
Trend illustrated
Infrastructure management platforms remain high-value targets because they can provide administrative access to entire environments.
#6 SolarWinds Web Help Desk Remote Code Execution
CVE-2025-26399
SolarWinds Web Help Desk contains an unauthenticated, insecure deserialization flaw in the AjaxProxy component that allows attackers to execute arbitrary commands on the host system.
This vulnerability is considered critical and is already being exploited in the wild.
Why it matters
The most dangerous vulnerabilities often share a common characteristic: no authentication required.
Because attackers do not need credentials, exploitation can be automated and scaled across many targets.
If exploited successfully, attackers could:
- Execute arbitrary commands
- Install malware
- Move laterally within the network
Organizations using this platform should treat this vulnerability as an urgent patch priority.
Trend illustrated
Attackers continue to prioritize unauthenticated remote code execution vulnerabilities, which enable rapid compromise of exposed services.
Patterns Across These Vulnerabilities
Although these vulnerabilities affect very different technologies, several important patterns emerge.
1. Active exploitation is now the norm
Most of the vulnerabilities above are already being exploited in real attacks. The window between disclosure and exploitation continues to shrink.
2. Control-plane infrastructure is a prime target
Platforms such as SD-WAN controllers, vCenter, and management tools represent high-leverage attack points that can expose entire environments.
3. Mobile and browser attack surfaces remain critical
Exploit chains targeting iOS and browser vulnerabilities demonstrate that endpoints remain a primary entry point for attackers.
4. Attackers favor scalable vulnerabilities
Unauthenticated RCE and widely deployed platforms allow threat actors to compromise large numbers of systems quickly.
What This Means for Security Teams
These vulnerabilities reinforce a broader reality in modern cybersecurity: the most dangerous flaws are not simply those with high severity scores, but those that combine three factors:
- Wide deployment
- Ease of exploitation
- High-privilege impact
For security teams, this means prioritizing exposure management rather than vulnerability counts. The organizations that respond fastest are those that can identify which vulnerabilities materially increase enterprise risk—and focus remediation efforts there.
As the volume of CVEs continues to grow, the ability to prioritize the few vulnerabilities that truly matter will increasingly determine how effectively organizations manage cyber risk.
SAFE brings order to the thousands of CVEs by moving away from “technical severity” (which is static) and toward “contextual risk” (which is dynamic). SAFE uses a 6-step automated engine to filter out the noise and find the small fraction of vulnerabilities that actually pose a financial threat to your business. Contact us to see a demo.