You answered all the questions – and created a paper trail for a negligence claim
By Grant Rexer and Jacqueline Lebo
Let’s talk about the elephant in the TPRM room: You can outsource your operations, but you cannot outsource your legal liability. When a third-party vendor suffers a data breach, regulators, plaintiffs, and cyber insurance providers don’t just look at what the vendor did wrong. They look directly at your organization and ask one critical question: Did you exercise adequate due diligence?
For years, the industry’s answer to that challenge has been 400-question spreadsheets. But here is the uncomfortable legal reality: if your overwhelmed team receives a massive questionnaire back from a vendor and “rubber stamps” it to push a deal through—without verifying claims or acting on missing controls—you haven’t reduced your liability. You’ve just created a paper trail of negligence.
In today’s litigious environment, anyone can be sued by anyone at any time. See below: The Wall of Legal Precedent.
A TPRM platform won’t grant you absolute legal immunity. However, how you conduct your vendor assessments is the difference between an indefensible negligence claim and proving a rigorous, systematic standard of care.
Here is how transitioning to an autonomous, AI-driven TPRM approach with SAFE helps transform your legal and regulatory posture.
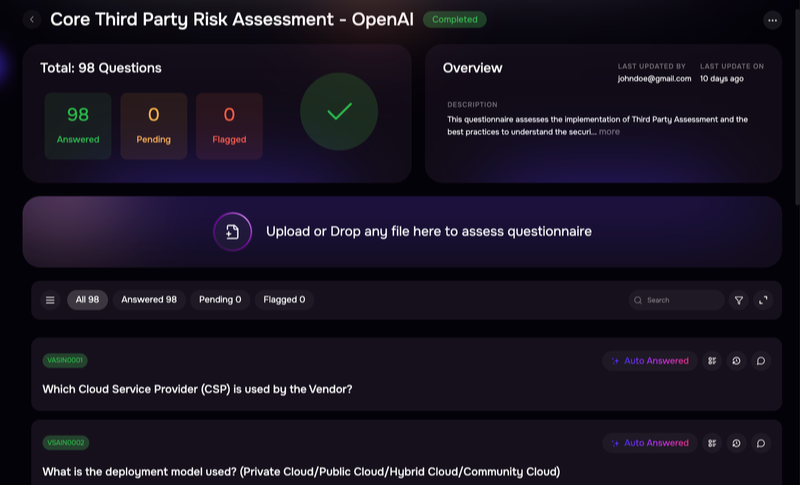
Vendor questionnaire assessment with SAFE TPRM
Shifting from “Point-in-Time” to Continuous Due Diligence
Regulators are increasingly losing patience with the “annual checkup” approach to third-party risk. A vendor might pass a static questionnaire in January, but if they suffer a critical vulnerability in March and you don’t catch it, your due diligence is fundamentally flawed.
This is where SAFE’s Agentic AI steps in. Instead of relying on manual, point-in-time assessments, SAFE deploys specialized AI agents (like our Monitoring and Outside-In Agents) that continuously track a vendor’s external attack surface, trust centers, and public breach data. If you are ever called into a boardroom—or a courtroom—you aren’t defending a year-old PDF; you are demonstrating active, 24/7 continuous monitoring.
Eliminating the “Arbitrary Assessment” Defense
Human reviewers get tired. When a single TPRM analyst (let’s call him Sam) has to manually review 50 spreadsheets a week, mistakes happen. Vendor A might get heavily scrutinized, while Vendor B slips through the cracks. In a legal discovery phase, this inconsistency looks like arbitrary oversight.
By automating intake, tiering, and evidence validation through SAFE’s autonomous workflows, you establish objective consistency. You can mathematically prove that your risk-scoring algorithms apply the exact same rigorous corporate security policy to every single vendor based on their tier and business context, completely removing human fatigue from the equation.
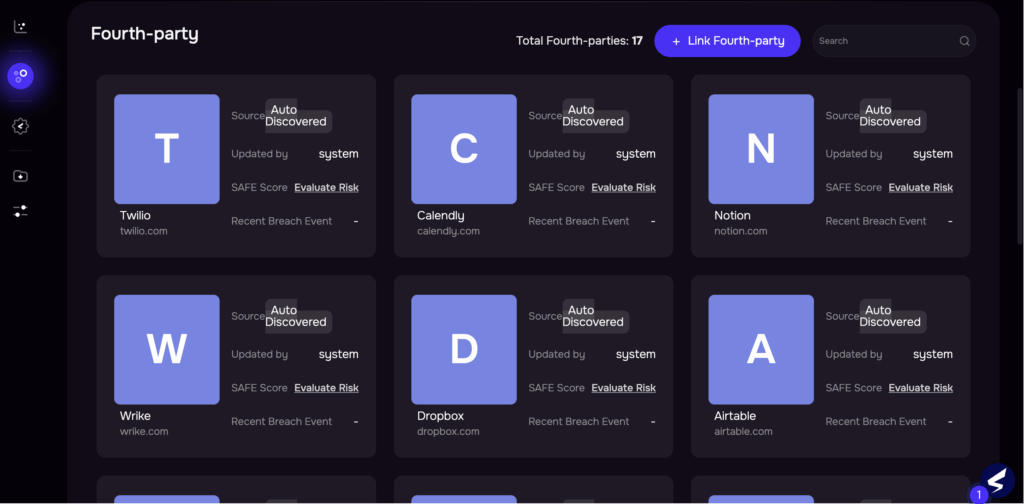
Fourth-party discovery with SAFE TPRM
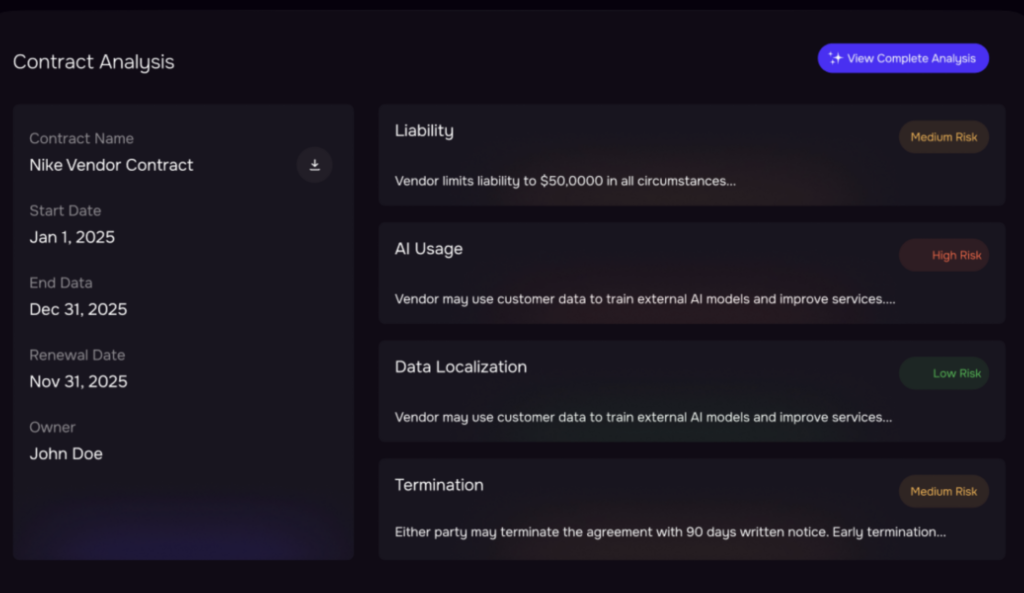
Vendor contract analysis with SAFE TPRM
The Power of the Immutable Audit Trail
If a downstream breach occurs, regulators like the FTC or state Attorneys General will demand the “receipts.” They want to see the timeline of what you knew and when you knew it.
SAFE TPRM acts as your system of record. Every action—from the moment our Contract Intelligence Agent analyzes an MSA, to the automated follow-up emails sent to vendors regarding missing controls, to the final approval—is logged. It provides an immutable audit trail proving that your company didn’t just file risk data away; you actively managed it.
Closed-Loop Remediation (Human-in-the-Loop)
The only thing legally worse than not finding a vendor risk is finding it and doing nothing about it. An automated tool that flags an issue is useless if there is no remediation.
SAFE’s Agentic AI is designed with a “Human-in-the-Loop” philosophy. The AI handles the heavy lifting—chasing vendors, extracting artifacts, and identifying gaps—but it serves those insights up for human validation. By using automated workflows to enforce vendor remediation before final approval is granted, you can prove that your organization actively closed the loop on identified vulnerabilities.
The Bottom Line
Let’s be clear: no software can guarantee you won’t face legal action if a vendor in your supply chain gets breached. The threat landscape is too complex, and the legal environment is too aggressive.
However, liability hinges on the concept of negligence. Operating a TPRM program based on manual spreadsheets, endless email chains, and rubber-stamped approvals is becoming increasingly difficult to defend.
By leveraging SAFE’s Agentic AI, you are doing more than just saving your analysts hundreds of hours. You are replacing subjective, manual friction with machine precision, continuous monitoring, and structured audit trails. You aren’t just assessing risk—you are building a legally defensible standard of care.

Dashboard – SAFE TPRM
The “Wall of Legal Precedent”
The question was: Did they exercise due diligence in third-party risk management?
- The AMCA Breach (Quest Diagnostics & LabCorp): In 2019, billing vendor AMCA was breached. Regulators didn’t just go after AMCA; they penalized Quest and LabCorp for failing to monitor their vendor’s security posture.
- Rady Children’s Hospital & Blackbaud: After cloud provider Blackbaud suffered a ransomware attack in 2020, plaintiffs sued the hospital, alleging they were negligent in failing to properly screen Blackbaud’s crisis management programs before handing over data.
- FTC v. GMR Transcription Services: The FTC held GMR liable when their contractor left files exposed. The verdict? GMR failed to verify that the vendor actually implemented the security practices they claimed to have.
- The MOVEit Supply Chain Breach (IBM & Colorado HCPF): In 2023, IBM was targeted in class-action lawsuits (like Wedeking v. IBM) because they were obligated to only hire vendors with adequate security. Failing to assess the tools in their own supply chain created a direct line of liability.
The Bottom Line
Whether it’s GDPR, HIPAA, or CCPA, you are the Data Controller. If your security team ignores a red flag in a questionnaire to speed up a contract or because they are understaffed or human error, you’re handing plaintiff attorneys their best evidence.
SAFE turns that “Security Theater” into actual risk reduction. We don’t just help you collect answers; we help you analyze them so your TPRM program isn’t just a paper shield—it’s a legal one. 🛡️✨
“A rubber stamp is just a fancy way of signing your own subpoena.”
Want to see how SAFE’s Agentic AI can transform your TPRM program from a compliance bottleneck into a defensible business enabler? See SAFE TPRM in Action or Schedule a 1:1 Demo


