A sophisticated attacker compromised a single AI integration. Millions of web applications felt the impact. Here is what every TPRM leader needs to know.

By SAFE Threat Research Team
Key Takeaways
- The Vercel breach originated from a compromised third-party AI tool (Context.ai), not from Vercel’s own systems.
- A threat actor claiming ShinyHunters affiliation listed stolen Vercel data including API keys, source code, and 580 employee records for $2 million in Bitcoin on BreachForums.
- Downstream exposure affected Web3, DeFi, and SaaS organizations hosting on Vercel, forcing emergency credential rotation across the ecosystem.
- The incident exposes three critical TPRM gaps: AI tool inventory blind spots, point-in-time assessment failures, and excessive third-party access permissions.
Overview
On April 19, 2026, Vercel the web infrastructure company behind Next.js and the deployment platform for millions of applications worldwide, confirmed unauthorized access to its internal systems. The breach was not the result of an unpatched CVE. It was not a brute-force attack against Vercel’s perimeter. It began with a third-party AI productivity tool called Context.ai.
This is the defining characteristic of the modern cyber threat landscape: the entry point is almost never the target itself. It is a trusted tool in the target’s extended ecosystem. And in 2026, as organizations accelerate AI tool adoption across every function, that ecosystem has never been larger or less carefully governed.
For security leaders responsible for third-party risk management, the Vercel breach is not just a news event. It is a case study. It illustrates exactly how rapidly an AI integration compromise can cascade into enterprise-level exposure, and it highlights the specific program capabilities that separate organizations that respond in minutes from those still assessing scope weeks later.
What Happened: The Vercel Breach Timeline
The Initial Compromise: Context.ai
Vercel disclosed that the breach originated when an attacker compromised Context.ai, a third-party AI tool used by one of Vercel’s employees. The attacker leveraged this compromise to take over the employee’s Google Workspace account. With access to the employee’s corporate identity, the attacker was able to navigate into Vercel’s internal environments.
Vercel described the attacker as “highly sophisticated based on their operational velocity and detailed understanding of Vercel’s systems.” The internal environments accessed included environment variables that were not designated as sensitive, a distinction that would become central to subsequent risk assessment communications.
The Data Claimed: A $2 Million Listing
Within hours, a threat actor claiming affiliation with the ShinyHunters cybercrime group posted on BreachForums offering what they claimed to be Vercel’s internal data. The listing included:
- NPM tokens and GitHub tokens
- API keys and deployment credentials
- Proprietary source code
- Database records and internal system data
- A file containing records for 580 Vercel employees, including names, email addresses, and account activity timestamps
The asking price was $2 million in Bitcoin, with an initial ransom demand of $500,000 reportedly floated directly to Vercel. Members of the ShinyHunters group publicly denied involvement, and Vercel has not independently confirmed the full scope of the data the attacker claims to possess.
Vercel’s Response
Vercel moved quickly to contain the incident. The company confirmed that environment variables designated as ‘sensitive’ were encrypted and showed no evidence of unauthorized access. CEO Guillermo Rauch stated that a supply chain analysis confirmed Next.js, Turbopack, and Vercel’s open-source projects remained safe.
The company issued guidance to affected customers: rotate secrets, monitor access to Vercel environments, and audit linked services. That guidance prompted an immediate response across the developer and Web3 ecosystem.
Why This Breach Has Industry-Wide Implications
The Scale of Vercel’s Deployment Footprint
Next.js, Vercel’s flagship framework, recorded more than 520 million downloads in 2025 alone. Vercel hosts frontends for wallet interfaces, decentralized exchanges, SaaS dashboards, and internal tools across virtually every sector of the digital economy. The platform sits inside the software delivery chain for an enormous number of organizations which means a breach at Vercel creates potential downstream exposure that extends far beyond Vercel’s own customer list.
The Supply Chain Attack Threat
The most serious concern raised by the security community in the immediate aftermath of the disclosure was not the data theft itself. It was the possibility that stolen deployment credentials GitHub tokens, NPM tokens, API keys could be used to inject malicious code into dependencies pulled by thousands of downstream applications.
This attack pattern, sometimes called a software supply chain attack, has been responsible for some of the most consequential security incidents of the past five years. When a platform this central to modern web development is breached, the question is not just what data was accessed. The question is whether the attacker has gained the ability to compromise the software that millions of users interact with daily.
Vercel’s confirmation that its open-source projects and supply chain were unaffected was a critical communication but it required customers to conduct their own assessments before that confidence could extend to their specific deployment environments.
The Immediate Ecosystem Response
The Web3 and DeFi ecosystem, which relies heavily on Vercel for frontend infrastructure, responded with immediate defensive action. Orca, the Solana-based decentralized exchange, confirmed it rotated every deployment credential as a precaution while verifying that on-chain funds and its core protocol remained unaffected.
The Cork Protocol CTO issued a warning urging users to pause interaction with DeFi applications hosted on Vercel, citing the concentration of crypto application frontends on the platform. This response while ultimately conservative given Vercel’s clarifications, illustrated the real operational cost of a significant third-party hosting provider incident.
The Third-Party Risk Anatomy of the Vercel Breach
To understand the TPRM implications of the Vercel incident, it is important to map the attack chain precisely. This was not a case of a vendor with weak perimeter security being directly compromised. It was a multi-hop attack that exploited trust relationships between tools, identities, and systems.
| Attack Chain Analysis Step 1: Context.ai (third-party AI tool) is compromised by threat actor Step 2: Attacker leverages Context.ai access to hijack Vercel employee’s Google Workspace account Step 3: Corporate identity access used to pivot into Vercel’s internal environments Step 4: Environment variables, API keys, and deployment tokens accessedStep 5: Data exfiltrated and listed for sale on BreachForums |
Gap 1: The AI Tool Inventory Blind Spot
Context.ai had access to an employee’s Google Workspace account. That level of access a third-party tool authorized to interact with corporate identity infrastructure should trigger a formal vendor risk assessment under any mature TPRM program. Yet most organizations today have no systematic inventory of the AI tools their employees are connecting to corporate accounts and systems.
The proliferation of AI productivity tools in 2025 and 2026 has outpaced most organizations’ vendor intake and onboarding processes. Employees connect AI writing assistants, coding tools, meeting summarizers, and productivity applications to their corporate Google, Microsoft, and Slack accounts as a matter of routine often without security review, procurement approval, or formal risk assessment.
Each of those connections represents a third-party integration with access to corporate identity infrastructure. Each is a potential attack vector of the type exploited in the Vercel breach.
Gap 2: Point-in-Time Assessment Failure
An annual vendor questionnaire for Context.ai even a thorough one completed six months before the breach, would not have detected the compromise or prevented the attack. Point-in-time assessments provide a snapshot of a vendor’s security posture at a single moment. They do not detect the dynamic changes, a vendor’s own breach, a change in access permissions, or anomalous usage patterns that indicate active exploitation.
The Vercel breach reinforces what security practitioners have understood for years but struggled to operationalize: continuous monitoring of third-party risk signals is not a nice-to-have capability. It is the foundational requirement for detecting the attack patterns that now dominate the threat landscape.
Gap 3: Excessive Access Without Ongoing Verification
The Vercel breach illustrates the consequences of over-permissioning third-party tools. When Context.ai was authorized to access the employee’s Google Workspace account, that access was granted based on the tool’s stated functionality and the employee’s assessment of its usefulness. The access was not regularly reviewed, scoped to the minimum required permissions, or subject to automatic revocation triggers.
Least-privilege access principles and regular access reviews for third-party integrations are not aspirational security hygiene. They are the controls that determine blast radius when a vendor is compromised. Had Context.ai’s access been scoped to the minimum required permissions and subject to regular review, the attacker’s ability to pivot from the tool compromise into Vercel’s internal environments would have been significantly constrained.
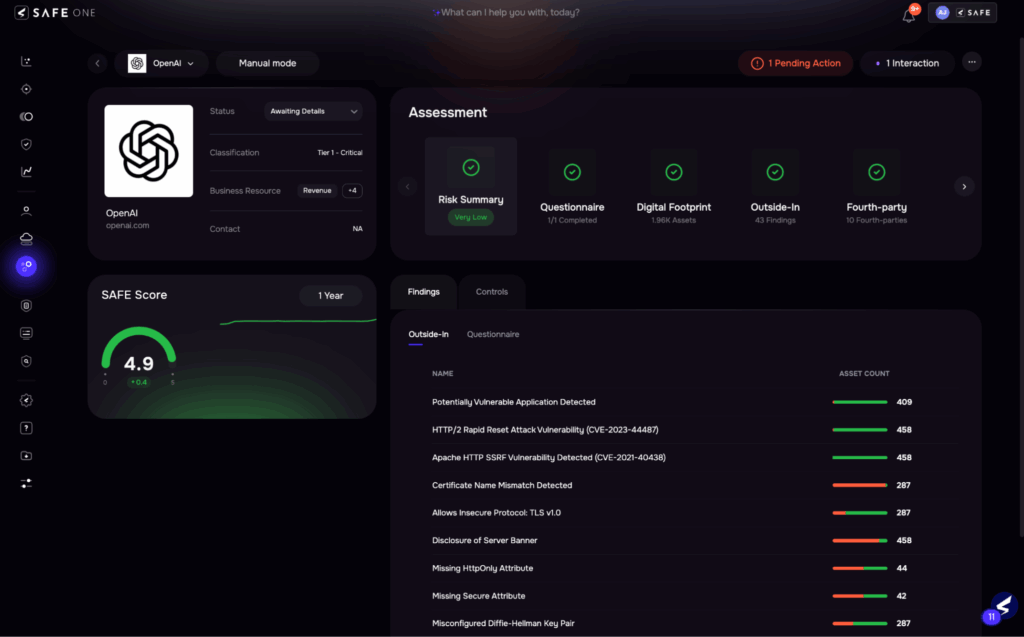
Vendor risk assessment, SAFE One Platform
The TPRM Program Capabilities That Made the Difference
Organizations that navigated the Vercel breach with minimal disruption shared specific program capabilities. These were not the result of heroic incident response. They were the result of program decisions made months and years before the incident occurred.
Complete Third-Party Integration Inventory
Organizations with comprehensive vendor inventories that included AI tool integrations were able to assess their exposure to the Vercel breach within hours. They knew which of their applications were hosted on Vercel. They knew which of their systems had third-party AI tools connected to corporate identity infrastructure. That visibility is the prerequisite for every other response capability.
Continuous Monitoring with Behavioral Signals
Continuous monitoring of third-party risk signals outside-in security assessments, dark web monitoring for vendor credential exposure, tracking of vendor security incidents provides the early warning capability that point-in-time assessments cannot deliver. Organizations with continuous monitoring programs received signals about the Vercel incident faster than those relying on vendor self-disclosure and industry news.
Credential Rotation Runbooks
The organizations that rotated credentials in hours rather than days had documented runbooks for doing so. They had identified their critical credentials in advance, established the rotation procedures for each, and assigned clear ownership. Emergency credential rotation is not a process that can be designed and executed simultaneously during an active incident. It must be prepared in advance.
Contractual Security Requirements
Mature vendor contracts include requirements for breach notification within defined windows often 24 to 72 hours as well as provisions for security audits, minimum security standards, and liability allocation. These contractual requirements create accountability mechanisms that informal vendor relationships lack.
The Broader Pattern: Why Third-Party and Supply Chain Risk Is the Defining Threat Vector
The Vercel breach is not an isolated event. It is the latest incident in a pattern of supply chain and third-party attacks that has defined the enterprise threat landscape for half a decade.
| Incident | Entry Vector | Target | Scale |
| SolarWinds (2020) | Malicious update in SolarWinds Orion | US Government agencies & Fortune 500 | 18,000+ organizations |
| MOVEit (2023) | Zero-day in MOVEit Transfer software | Organizations using MOVEit for file transfer | 2,500+ organizations, 90M+ records |
| XZ Utils (2024) | Malicious code injected in open-source compression library | Linux distributions globally | Potential global infrastructure impact |
| Vercel (2026) | Compromised third-party AI tool (Context.ai) | Vercel internal systems and environment variables | Millions of downstream applications at risk |
The pattern is consistent across all four incidents. The attacker’s target was not the entry point. The entry point was a trusted third party or component in the target’s ecosystem. And in every case, the organizations with mature third-party risk programs, continuous monitoring, complete vendor inventories, and tested response runbooks were substantially better positioned to detect, contain, and recover from the incident.
Frequently Asked Questions
What was the Vercel breach and when did it happen?
The Vercel breach was disclosed on April 19, 2026. Vercel confirmed unauthorized access to its internal systems after an attacker compromised Context.ai, a third-party AI tool used by one of
its employees. The attacker used that access to take over the employee’s Google Workspace account and pivot into Vercel’s internal environments.
What data was stolen in the Vercel breach?
A threat actor on BreachForums claimed to have stolen API keys, NPM tokens, GitHub tokens, source code, database records, and employee data including records for 580 Vercel employees. These claims have not been fully independently verified. Vercel confirmed that sensitive environment variables those designated as such and protected by encryption showed no evidence of unauthorized access.
What is a third-party risk in the context of the Vercel breach?
In the Vercel breach, third-party risk materialized when an employee’s use of a third-party AI tool (Context.ai) created an attack vector into Vercel’s own systems. Third-party risk is the potential for an organization to suffer a security incident or data breach as a result of a compromise, failure, or vulnerability at a vendor, supplier, tool provider, or service provider with access to the organization’s systems, data, or infrastructure.
How does the Vercel breach demonstrate supply chain risk?
The Vercel breach demonstrates supply chain risk in two ways. First, the attacker entered Vercel’s systems through a compromised third-party tool a classic supply chain attack vector. Second, because Vercel hosts frontends for thousands of organizations, a breach at Vercel creates potential downstream exposure for every organization that relies on Vercel-managed deployment infrastructure. This second layer the risk that Vercel’s compromise could be leveraged to compromise Vercel’s customers is fourth-party risk.
What should organizations do in response to the Vercel breach?
Organizations should immediately audit which of their applications are hosted on Vercel, review which environment variables stored in Vercel are sensitive or could provide access to internal systems, rotate API keys and deployment credentials for all Vercel-hosted applications, and assess whether any of their employees are using third-party AI tools with access to corporate identity infrastructure that have not been formally risk-assessed.
How can a TPRM program prevent AI tool-based attacks?
A mature TPRM program can reduce exposure to AI tool-based attacks by maintaining a complete inventory of all third-party tool integrations, including employee-initiated AI tools connected to corporate accounts; requiring formal risk assessment for tools with access to corporate identity infrastructure; enforcing least-privilege access for all third-party integrations; implementing continuous monitoring for anomalous third-party access patterns; and establishing documented procedures for rapid credential rotation when a vendor incident is disclosed.
Conclusion: Third-Party Risk Is No Longer Optional to Manage
The Vercel breach arrived at a moment when AI tool adoption is accelerating across every function of every organization. Every new AI integration is a new third-party relationship. Every new third-party relationship is an extension of your attack surface. And in 2026, that attack surface includes not just your direct vendors, but the tools your vendors’ employees are using to do their jobs.
Your organization’s security posture is a function of your entire ecosystem not just the controls you directly manage. The Vercel breach makes this concrete. A third-party AI tool used by a single employee at a single vendor created potential downstream exposure for millions of applications worldwide.
The organizations that managed this incident well were not lucky. They had continuous monitoring in place. They had credential rotation runbooks ready to execute. They had clear visibility into which of their critical operations depended on Vercel-hosted infrastructure. They had governance policies that covered third-party AI tool usage. That is what mature third-party risk management delivers.
If the Vercel breach revealed gaps in your organization’s TPRM program, the response is not to conduct more vendor questionnaires. It is to build the continuous monitoring, governance, and operational readiness capabilities that turn incidents like this from crises into manageable events.

TPRM Dashboard, SAFE One
How SAFE One Addresses Third-Party AI Risk
SAFE One’s TPRM module provides the continuous monitoring, outside-in risk assessment, and real-time vendor visibility that the Vercel breach demonstrates are essential for modern third-party risk management. SAFE One goes beyond point-in-time questionnaires to deliver
- Continuous outside-in monitoring across your entire vendor ecosystemAutomated intake and onboarding with tiered risk assessment workflows
- Real-time vendor interaction and remediation tracking
- Dashboards and reporting that give TPRM leaders and executives the visibility they need to act