Vulnerabilities in Windows LNK, Adobe Acrobat, Android Framework and more are actively exploited.

By SAFE Threat Research Team
This week’s trending vulnerabilities span phishing campaigns targeting national infrastructure, zero-authentication remote code execution in developer tooling, and an actively exploited zero-interaction Android flaw. Below are the six CVE clusters your security team should have eyes on right now — and why each one is gaining traction in the wild.
1. Windows LNK / Archive Execution Chain (CVE-2025-6218, CVE-2025-8088)
Vulnerable Component: Microsoft Windows (LNK / archive execution chain)
These two CVEs are actively being exploited in UAC-0226 campaigns targeting Ukrainian organizations through weaponized RAR archives containing decoy documents. The attack chain relies on minimal user interaction: it typically extracts the archive and executes a disguised shortcut file, which triggers a multi-stage PowerShell-based payload delivered directly to memory.
What makes this cluster especially dangerous is its combination of reliable phishing delivery, fileless execution, and strong evasion techniques. Because the malicious code runs in memory rather than writing to disk, traditional endpoint detection based on file signatures offers limited protection.
Security teams should enforce stricter controls on archive handling, monitor LNK execution patterns, and ensure enhanced visibility into script execution across endpoints.
2. Adobe Acrobat Prototype Pollution RCE (CVE-2026-34621)
Vulnerable Component: Adobe Acrobat Reader / Acrobat
A prototype pollution vulnerability in Adobe Acrobat Reader may allow arbitrary code execution under specific conditions when a specially crafted PDF is opened. The issue stems from improper handling of JavaScript objects in the PDF execution environment, allowing attackers to manipulate object properties and potentially execute code via crafted payloads. This CVE is already being reported as actively exploited in phishing campaigns.
While exploitation requires user interaction, the attack vector is highly effective due to the widespread use of Acrobat in enterprise environments and the continued success of phishing-based delivery. This vulnerability highlights the continued risk of document-based initial access, where trusted file formats are used to execute malicious scripts. Organizations should prioritize patching Acrobat across endpoints, restrict or disable JavaScript execution where not required, and monitor for suspicious child processes spawned by Acrobat (e.g., PowerShell or command-line utilities).
3. Marimo Python Notebook Unauthenticated RCE (CVE-2026-39987)
Vulnerable Component: Marimo Python Notebook Platform
This one is trending fast. An unauthenticated remote code execution vulnerability in Marimo’s WebSocket terminal endpoint — resulting from missing authentication — allows arbitrary command execution on any exposed instance. Exploitation was observed rapidly after public disclosure.
Exploitation requires no credentials or user interaction, significantly lowering the barrier to compromise. Public proof-of-concept activity and exploitation attempts emerged rapidly after disclosure, highlighting the risk of exposing developer tooling directly to the internet.
Environments running notebook platforms often contain sensitive data, API keys, and access to production systems, making this a high-impact target even outside traditional attack surfaces. Organizations should immediately restrict external access to Marimo instances, bind services to localhost where possible, and enforce authentication through reverse proxies or access control mechanisms.
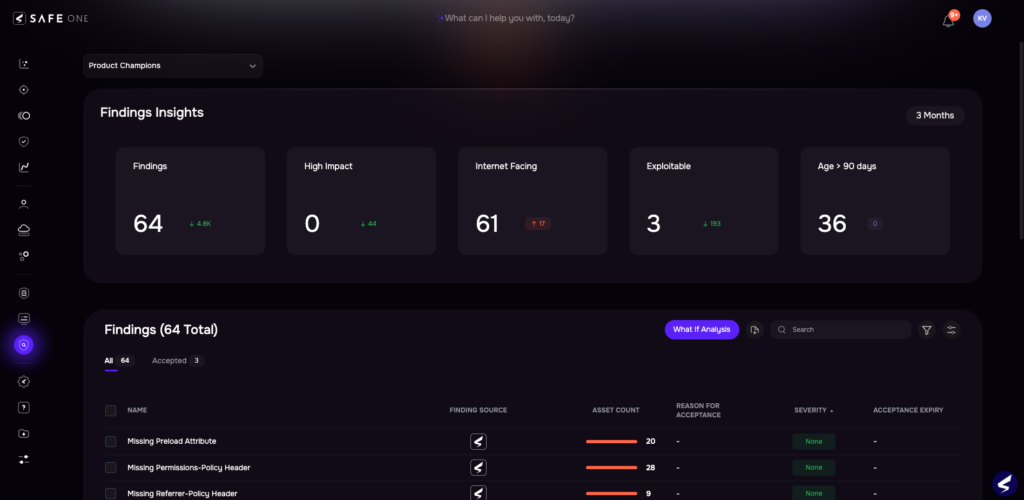
Vulnerabilities tracking in the Findings Center of the SAFE One platform
4. Apache ActiveMQ Classic Jolokia API Abuse (CVE-2026-34197, CVE-2024-32114)
Vulnerable Component: Apache ActiveMQ Classic (Jolokia API)
Attackers are actively targeting exposed Jolokia management endpoints in Apache ActiveMQ Classic deployments. When improperly secured, these endpoints can be used to query sensitive data and invoke MBean operations remotely.
Issues associated with Jolokia exposure and related ActiveMQ vulnerabilities (including CVE-2026-34197 and CVE-2024-32114) can be chained with other exposed interfaces to achieve a deeper compromise. In certain configurations, this may enable remote code execution through unsafe MBean operations or auxiliary endpoints.
Given ActiveMQ’s role in enterprise messaging and data pipelines, exposed management interfaces present a high-impact risk, potentially enabling data exfiltration, service disruption, or lateral movement. Organizations should audit all deployments for externally accessible Jolokia endpoints, restrict access to trusted networks, enforce strong authentication, and disable Jolokia where it is not required.
5. Flowise AI Platform CustomMCP Node RCE (CVE-2025-59528)
Vulnerable Component: Flowise AI Platform (CustomMCP node)
A remote code execution vulnerability in Flowise’s CustomMCP node results from improper handling of user input, enabling arbitrary JavaScript execution for users with API access. This CVE is actively being exploited against exposed Flowise instances.
The stakes here are particularly high: Flowise is an AI pipeline orchestration platform, meaning a successful exploit grants access not only to the underlying server but potentially to the AI workflows, model endpoints, external API integrations, and sensitive data that run through it. In environments where API access is exposed or poorly controlled, this vulnerability provides attackers with a remarkably powerful foothold. Flowise deployments should be patched immediately and access restricted to authenticated, authorized users only.
6. Android Framework Zero-Interaction DoS (CVE-2026-0049)
Vulnerable Component: Android Framework
This vulnerability in the Android Framework can be triggered without any user interaction to cause denial-of-service conditions, impacting system stability and availability across modern Android versions. It is actively being exploited in the wild.
While CVE-2026-0049 does not enable code execution, reports indicate in-the-wild exploitation, highlighting a growing focus on availability disruption as a standalone objective. Repeated triggering of such vulnerabilities may result in persistent crashes or forced reboots, potentially creating conditions for follow-on attacks.
The lack of required user interaction significantly increases exposure, as exploitation does not rely on phishing or user-driven actions. Organizations managing Android device fleets should prioritize applying vendor patches through MDM platforms and ensure devices remain on supported security update levels.
What to Do Now
This week’s trending vulnerabilities cut across phishing, unauthenticated RCE, AI platform exposure, and zero-interaction exploitability — a broad attack surface that rewards defenders who prioritize based on active exploitation signals rather than CVSS scores alone. Key actions for security teams:
- Patch immediately: Adobe Acrobat (CVE-2026-34621), Marimo (CVE-2026-39987), and Flowise (CVE-2025-59528) are all being actively exploited post-disclosure.
- Audit exposed services: Jolokia endpoints on ActiveMQ brokers and any internet-facing Marimo or Flowise instances should be locked down or taken offline.
- Harden email pipelines: The Windows LNK/archive chain (CVE-2025-6218, CVE-2025-8088) is being used in phishing delivery — archive file filtering and PowerShell controls are your first line of defense.
- Apply Android patches via MDM: CVE-2026-0049 requires no user interaction, making fleet-wide patch enforcement the only reliable mitigation.
Staying ahead of trending exploitation requires continuous monitoring of threat actor activity, not just patch Tuesday releases. The vulnerabilities attackers are actively weaponizing today are often not the highest-severity CVEs on paper — they’re the ones that combine ease of exploitation with high-value targets and reliable delivery.
About SAFE
SAFE automates your TPRM lifecycle from onboarding through risk assessment and continuous monitoring. Watch the video: SAFE TPRM in Action.