Drives cyber resilience up while bringing down insurance costs
THE CHALLENGE
Carvana relied on multiple scanners, making it difficult to consolidate asset and vulnerability data. This created operational overhead, blind spots, and challenges in prioritizing vulnerabilities and communicating risk.
THE RESULTS
enterprise breach likelihood
in insurance premiums
in < 9 months of operationalization
Get Measurable Impact
with SAFE CTEM
Reduction in Critical Exposures on a Daily Basis
Reduction in Mean Time to Remediate (MTTR)
Productivity improvement for triage, ticketing & validation
Autonomous CTEM to Manage Exposure Risk
Unified Risk Visibility
Create a single, trusted exposure inventory of assets and exposures from tools that already exist in your environment
Risk-Based Prioritization
Move away from CVSS scores. Prioritize exposures based on exploitability, threat intelligence, and business impact
Scaled Exposure Management
Continuously reduce exposure across complex environments with agentic workflows that keep teams aligned
SAFE Drives Action, Not Just Insight
Across Your CTEM Lifecycle
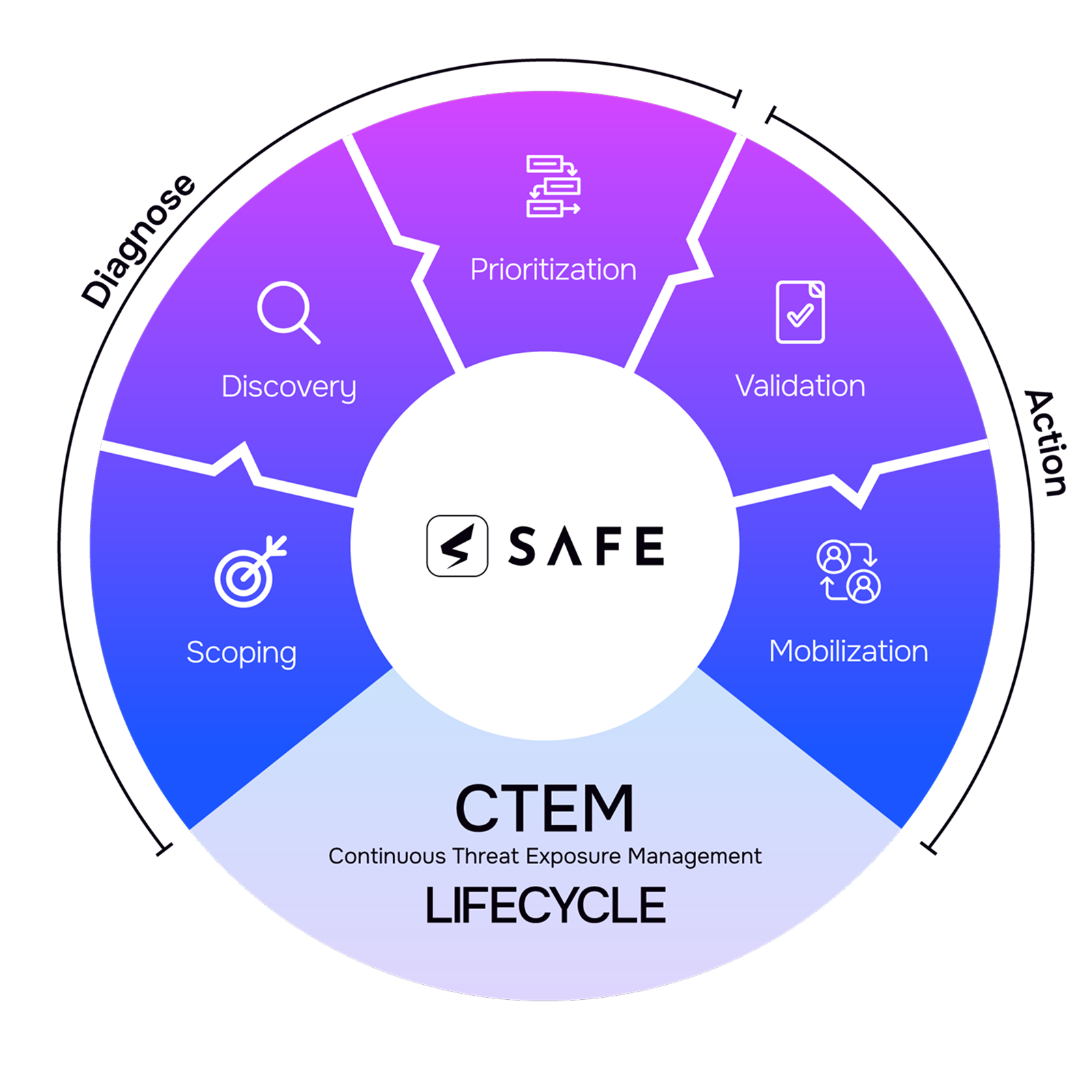
De-Risk Your Critical Exposures with SAFE CTEM
Context-Driven
Scoping
Bring all your exposure data in one unified and intelligent system
- Define CTEM scope by aligning exposure monitoring to business-critical assets, crown-jewels, and more
- Build a clear, consistent risk terminology across Security, Risk, and IT teams based on financial impact
- Reduce noise and lay a strong foundation for discovery by normalizing data across available security tools
Discover Your Exploitable Attack Surface
Focus effort on exposures that actually increase breach risk
- Pull live data from 200+ integrations across vulnerability tools, pen tests, SAST, DAST, CMDBs, and more
- Aggregate, normalize and de-duplicate vulnerability and asset data from scanners and tools you already have
- Continuously uncover new assets, services, and identities as the environment evolves with custom Agentic workflows
Risk-Based Exposure Prioritization
Allocate resources smartly to manage the most critical exposure first
- Incorporate business context into exposure decision, ensuring the most critical assets and systems are protected first
- Automate the analysis of the impact of threat intelligence and compensating controls, mitigations, and business criticality
- Enrich findings with AI pipeline and map to key intelligence indicators such as CISA KEV, EPSS, MITRE ATT&CK, CWE
Exposure Validation & Risk Confirmation
Cut false positives to focus on the 1-5% of truly exploitable gaps
- Validate which exposures attackers can weaponize by incorporating attack path analysis, breach simulation, and more
- Confirm whether existing controls reduce attack risk by evaluating the effectiveness of EDR, firewalls, WAFs, etc
- Refine exposure prioritization using validated risk signals, so teams focus remediation on confirmed high-impact exposures
Agentic Workflow-driven Mobilization
Drive coordinated remediation action across owners to reduce exposure risk
- Mobilize remediation when high-risk exposures are identified and notify teams with Agentic Asset Ownership workflows
- Coordinate remediation across security and IT systems with customizable Agentic workflows that create and route tickets
- Govern remediation with structured exception management, ensuring unresolved risks are tracked, justified, and monitored
Agentic KEV & Zero-Day Response
Stay on top of real-world threats as they emerge with continuous visibility
- Continuously track known exploited vulnerabilities and emerging zero-days using real-time threat intelligence signals
- Build agentic workflows that automatically re-prioritize exposures as new KEVs are disclosed
- Leverage agentic response workflows to orchestrate a fast and coordinated response with clear ownership
Dashboards and Reporting
Prove control coverage, show progress, and stay audit-ready
- Give executives a clear view of exposure posture and remediation progress with real-time dashboards
- Generate instant reports which map exposures and controls to frameworks like NIST, ISO 27001, CIS, and PCI DSS
- Leverage Agentic workflows such as PCI Exposure Management to maintain compliance-level visibility
AI You Can Trust for Cyber Risk Decisions
Powered by SAFE AURA
SAFE NAMED A VISIONARY
Gartner® Magic Quadrant™ for Exposure Assessment Platforms, 2025
Take SAFE for a Test Drive
TEST DRIVE SAFEFrequently Asked Questions
-
How does SAFE automate Continuous Threat Exposure Management (CTEM)?
-
SAFE automates CTEM using agentic workflows and AI-driven reasoning to continuously discover exposures, prioritize risks, validate exploitability, and coordinate remediation. Instead of relying on manual triage and disconnected tools, SAFE correlates asset and vulnerability data across security platforms, evaluates exploitability and business context, and automatically triggers the appropriate remediation and governance actions. This allows security teams to continuously reduce exposure risk while scaling CTEM execution across complex environments.
-
What exposure management challenges does SAFE CTEM solve?
-
SAFE CTEM addresses common exposure management challenges such as fragmented asset visibility, vulnerability overload, inconsistent prioritization, and slow remediation coordination. By unifying exposure data across security tools and applying exploitability-aware prioritization, SAFE helps teams focus on the exposures attackers are most likely to exploit and drive faster, more coordinated remediation across the organization.
-
How long does it take to implement SAFE CTEM and start seeing value?
-
Most organizations can operationalize SAFE CTEM within weeks. SAFE integrates with existing security tools to ingest asset and vulnerability telemetry and automatically normalizes and de-duplicates exposure data. From there, teams can use Agentic workflows to immediately begin prioritizing exploitable risks and coordinating remediation workflows. Many organizations begin seeing improvements in exposure visibility and remediation focus within the first few weeks.
-
Can SAFE CTEM integrate with our existing security tools?
-
Yes. SAFE CTEM integrates with a wide range of security and IT platforms, including vulnerability scanners, cloud security tools, endpoint detection platforms, asset inventories, and ticketing systems. These integrations allow SAFE to continuously ingest exposure data across the security stack, creating a unified exposure inventory that supports accurate prioritization and remediation orchestration.
-
What are agentic workflows and how do they help in CTEM?
-
Agentic workflows are AI-driven workflows that autonomously orchestrate exposure management processes. In SAFE CTEM, these workflows automate tasks such as exposure prioritization, remediation ticket creation, ownership assignment, and governance tracking. By continuously evaluating exposure data and triggering actions based on defined policies, agentic workflows help organizations scale CTEM programs without increasing operational overhead.
-
How does SAFE measure CTEM success and exposure reduction?
-
SAFE measures CTEM success by tracking changes in exposure state over time rather than relying solely on vulnerability counts or ticket closure metrics. By continuously monitoring asset lifecycle changes and remediation outcomes, SAFE provides clear visibility into exposure reduction trends and helps organizations demonstrate measurable improvements in their security posture.
-
How is SAFE CTEM different from traditional vulnerability management tools?
-
Traditional vulnerability management tools generate large volumes of findings and prioritize them primarily using severity scores. SAFE CTEM builds on SAFE’s leadership in Cyber Risk Quantification (CRQ) to help vulnerability management teams prioritize and reduce exposure based on financial impact, not just technical severity. By unifying exposure data across security tools and evaluating exploitability using threat intelligence, environmental context, asset state, and control coverage, SAFE identifies the exposures that matter most and quantifies their potential business impact in dollar terms. This enables organizations to focus remediation on the risks that truly threaten the business rather than chasing thousands of scanner alerts.
Latest from SAFE
Discover Why Continuous Threat Exposure Management (CTEM) is a Top 10 Security Trend
CTEM shifts cybersecurity from managing vulnerabilities to reducing real-world exposure continuously.
Learn More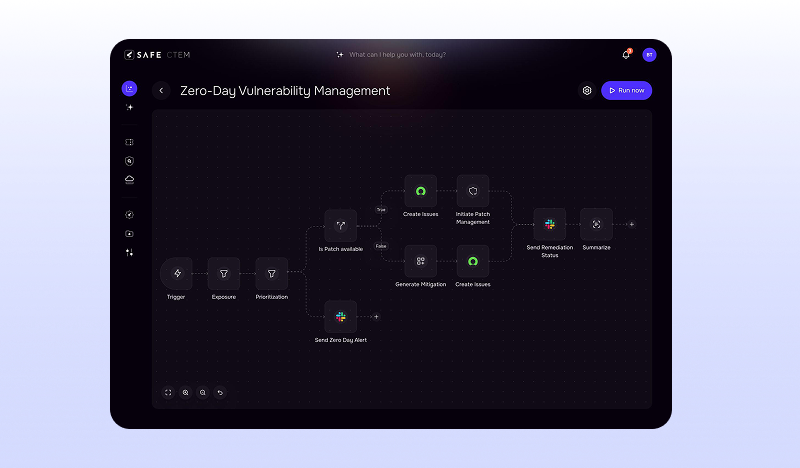
Autonomous Continuous Threat Exposure Management To Manage Exposure Risk
SAFE CTEM shifts exposure management from tracking what’s vulnerable to focusing on what’s exploitable.
Learn More
SAFE named a Visionary in Gartner® Magic Quadrant™ for Exposure Management (2025)
SAFE CTEM, an AI-native Cyber Risk and Exposure Management platform, provides measurable exposure reduction.
Learn More















